cPanel, the server and website management software used by millions of domains and hundreds of thousands of companies, has a critical vulnerability, CVE-2026-41940, that is under active exploitation.
The CVSS 9.8 cPanel vulnerability lets attackers bypass authentication. It affects “all currently supported versions after 11:40,” cPanel said in a short advisory, being updated in real-time as The Stack published today.
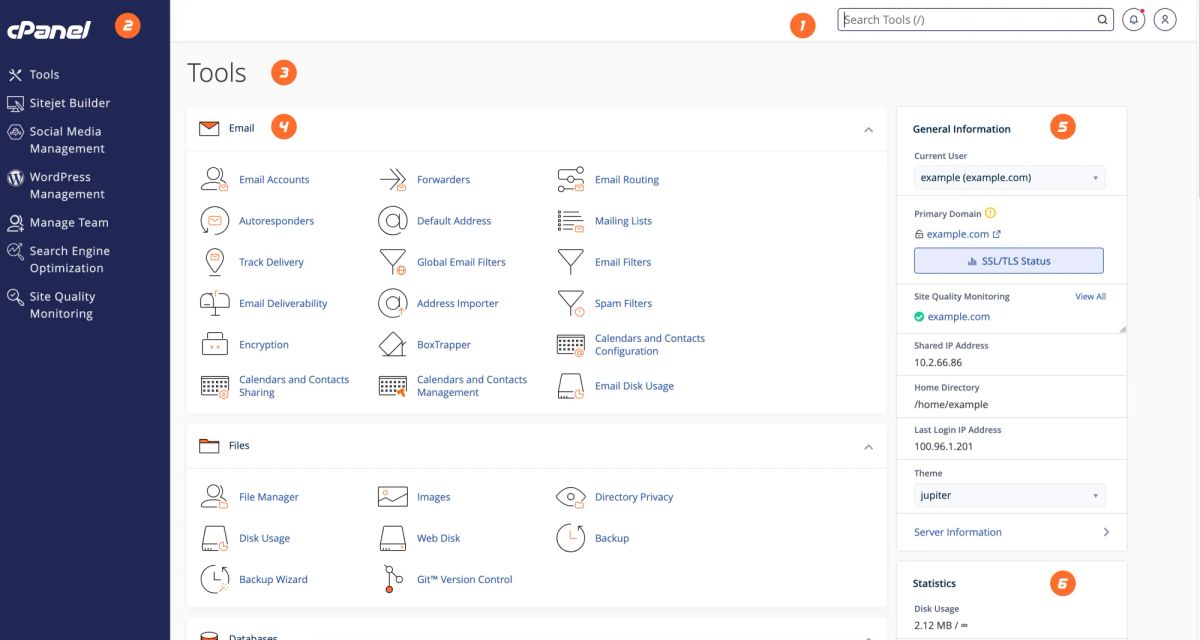
WHM, the administrative interface used to manage, monitor, and control multiple cPanel accounts, is also vulnerable to the CVSS 9.8 bug.
cPanel and WHM (management ports 2083, 2087) are usually exposed to the internet so that admins can manage their sites, and attacks require no user interaction; an attacker simply sends specifically crafted HTTP requests directly to the server. The vulnerability chains multiple small, seemingly minor logic flaws together to give a remote user root access.
Privately owned cPanel's team urged the Internet's millions of cPanel users in its advisory to "force password reset for root and all WHM users; audit /var/log/wtmp and WHM access logs for unauthorized access; [and] check for persistence mechanisms (cron, SSH keys, backdoors)."
Updating the thin advisory moments before The Stack published, cPanel provided a detection script to look for indicators of compromise (IOCs).
The CVE has not yet hit CISA's KEV.
Managed hosting provider KnownHost's CEO Daniel Pearson said that attacks may have been ongoing since February this year. (The Stack could not immediately confirm post-compromise attacker behaviour.)
He wrote today on Reddit: “This has absolutely been used in the wild…
“I've personally confirmed the access, and the exploit has been re-created. We're not releasing any of that information externally at this time as the last thing the industry needs is a bunch of copycats trying it out.”
Pearson did not share IOCs but suggested that users check their WHM (a control panel used by hosting providers to manage cPanel accounts) access log and session log “for successful root sessions coming from IPs you aren't aware of or shouldn't have access to your system. Also check for access specifically to the WHM Root Terminal/SSH interface page.”
Benjamin Harris of attack surface management firm watchTowr, commented: “Within hours of the advisory dropping, nearly every major hosting provider on the planet had firewalled their own customers off their own product. Hosting.com, Namecheap, KnownHost, HostPapa, InMotion and the rest all pulled the emergency brake because the alternative was watching their entire customer base get owned in real-time…”
cPanel has pushed a patch; all versions below are safe.
- 11.110.0.97
- 11.118.0.63
- 11.126.0.54
- 11.132.0.29
- 11.136.0.5
- 11.134.0.20
- WP Squared 11.136.1.7
cPanel users can confirm they are on a patched version of cPanel with the following command: /usr/local/cpanel/cpanel -V and if it doesn’t match one of the versions above, well, then patch up pronto before things get heated.
We keep our infosec reporting free out of public interest. Throw us a bone through a paid membership (£25/m, or £250/y); it helps us keep doing it, and also gets you a 75% discount on our events. (Next up, attack surface management talk and beers on us in London, May 26; more to follow...)
