
When is help desk software also remote access software for hackers?
When it’s SolarWinds Web Help Desk, built on WebObjects
<Deafening silence/>
Right, that’s just not hysterically funny.
Nor, arguably, is the news that that pre-auth RCE vulnerability CVE-2025-26399 is being exploited in the wild – and that it is, in SolarWinds’ own words, a “patch bypass of CVE-2024-28988, which in turn is a patch bypass of CVE-2024-28986…” It’s turtles patch bypasses all the way down.
(You patched, back in September 2025, though, right?)
SolarWinds Web Help Desk includes the likes of asset management, incident tracking, ticket management, workflow automation and other tools.
This “represents a logically attractive target for attackers. Ticketing systems are often exposed to large numbers of users, are frequently internet-facing, and contain large volumes of sensitive internal data,” as watchTowr noted.
SolarWinds pushed a patch for CVE-2025-26399 (added to CISA’s KEV today) back in September 2025. The bug affects 12.8.7 and all previous versions.
Legacy WebObjects code to blame…
The Big, Fat, Ugly problem here is that this widely used software was built on a Java web framework, WebObjects, that was defunct decades ago.
As attack surface management firm watchTowr noted in a rather cutting look at the product’s code-underpinnings last month, SolarWinds’ product security folks face having to secure “an application built on legacy WebObjects code that exposes an AjaxProxy component capable of materializing attacker-controlled objects and invoking methods with them…
“From a security perspective, that is a difficult foundation to defend.”
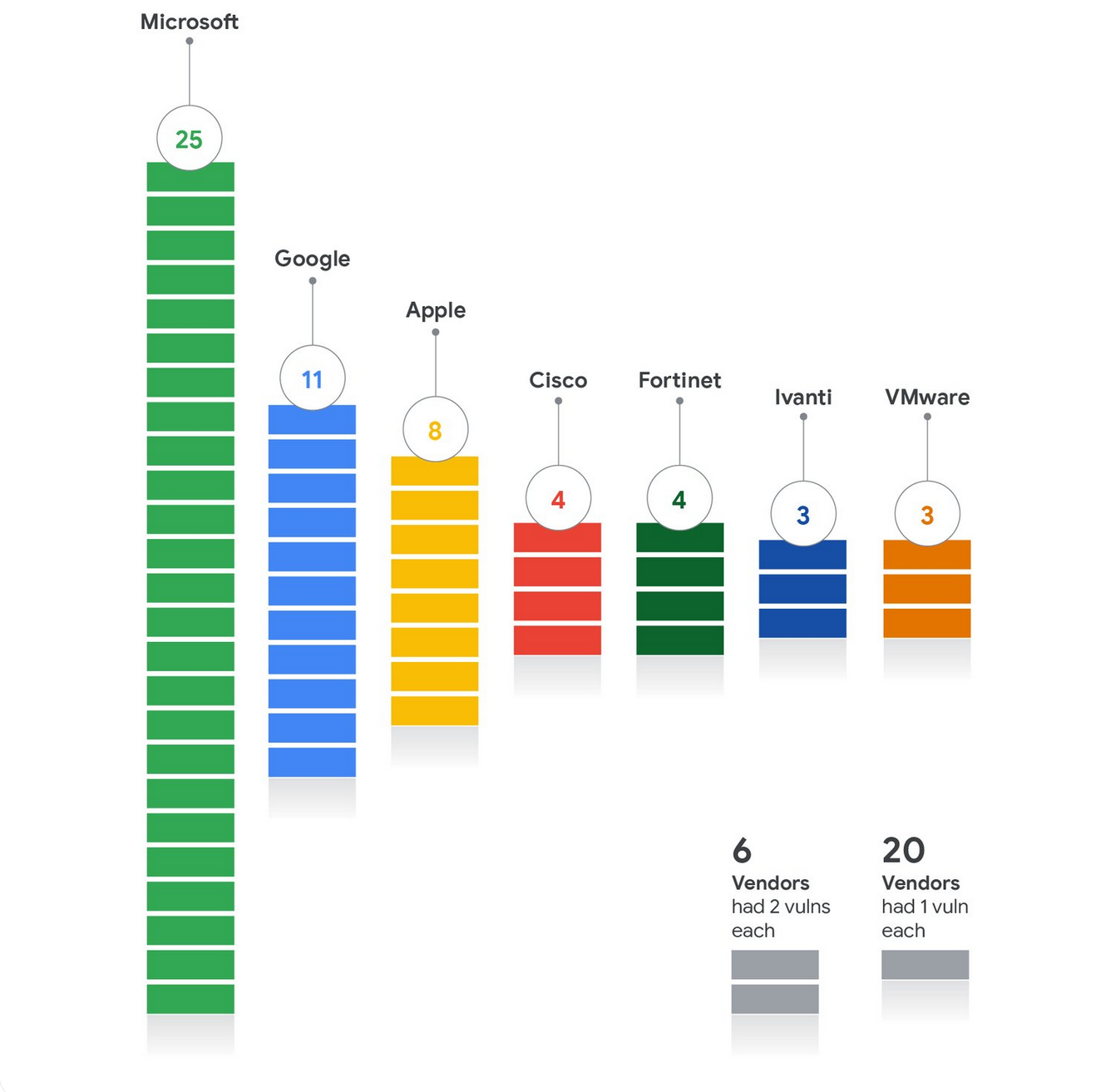
Legacy codebases continue to plague everyone from Microsoft to Ivanti to Fortinet – just three of the seven organisations that had the most zero days exploited in their products in 2025, and which have a “demonstrable history” of repeatedly exploited legacy code underpinning their platforms.
(See below, credit GTIG.)
Efforts to patch bugs in them faster than attackers can find new ones continues to be a white hat versus black hat game of whac-a-mole.
Similar examples at Redmond include the way in which the legacy MSHTML system embedded in Windows continues to be a nexus for attacks.
(Witness, for the prosecution, the recently exploited CVE-2026-21513, CVE-2025-33053, CVE-2025-30397, and CVE-2024-38112… We await news of more exploited MSHTML bugs every Patch Tuesday with interest.)
Or, perhaps, the way Ivanti Pulse Secure appliances were found recently to be running on a base operating system of CentOS 6.4 which is 11-years old and no longer supported; a creaking heart surrounded by software libraries vulnerable to a reported 973 flaws; 111 with publicly known exploits…
(That’s “more vulnerable shell scripts than we have time or resources to fully investigate,” as Eclypsium’s Nate Warfield put it back in early 2024.)
Ivanti’s then-CEO Jeff Abbott subsequently promised “stack modernization of our Network Security products… [with] isolation and anti-exploit technologies to reduce the potential impact of future software defects.”
Microsoft, meanwhile, has been chipping away at its stack via a sweeping “Secure Futures Initiative,” which includes ripping out tens of thousands of legacy tenants and rewriting everything that’s not nailed down in Rust.
All of the past five SolarWinds vulnerabilities added to KEV were in the Web Help Desk product, suggesting a threat group or individual has got the bit between their teeth when it comes to punching 0day-shaped holes in it.
The Stack has asked SolarWinds what it is doing, structurally, to shore up product security, and will update this article when we have an answer.
