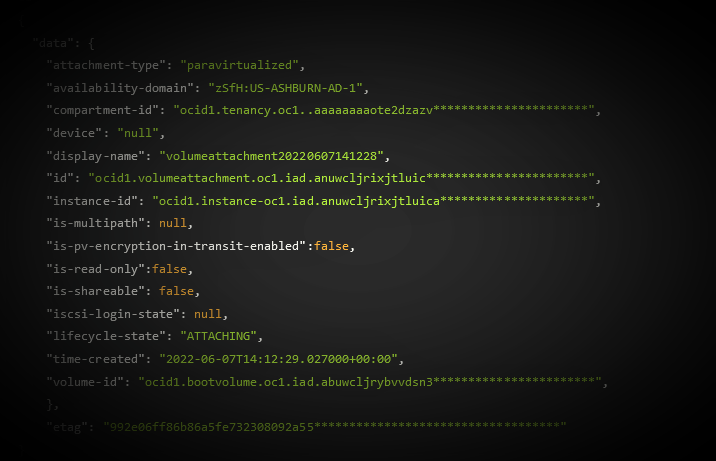
Oracle Cloud Infrastructure (OCI) had a critical tenant isolation vulnerability that would have allowed an attacker to gain read/write access to the disks of other customers, owing primarily to the lack of permissions verification in a storage expansion API. The bug was in OCI’s AttachVolume API. It was not immediately clear when the vulnerability was introduced. It was patched in July by Oracle within 24 hours of disclosure.
The bug let an attacker add a virtual disk to any compute instance within their availability domain (local region) without permission, do so across tenancies, see and influence any activity in it.
The vulnerability was reported by Israeli cloud security startup Wiz, which has also exposed severe cross-tenant vulnerabilities in Azure on multiple occasions. (It has also found thousands of AWS customer databases exposed by scanning for CIDR blocks – specific IP addresses – from within the cloud provider and then port scanning them; an issue in that case down to customer misconfiguration and not a cross-tenant isolation failing.)
Oracle “responded extraordinarily quickly” to the disclosure of the vulnerability – which Wiz is calling AttachMe – the security company said today. Within “24 hours of being informed by Wiz, Oracle patched #AttachMe for all OCI customers. No customer action was required” the company said in a blog detailing the vulnerability.
Oracle cloud vulnerability
Wiz engineers found that “attaching a disk to a VM in another account didn’t require any permissions. This means a potential attacker could have accessed and modified data from any OCI customer, and in some cases even take over the environment” – the attacker would have had to know the ID of a target victim’s instance or gained it from a low-privileged user machine and be in the same Availability Domain (AD) to exploit the bug.
Oracle’s rapid reaction compares favourably to Azure’s response to a Wiz disclosure in January 2022.
That saw it take two months and “several escalations, for MSRC to notify us that they had fixed the reported issue” and after that fix, “ the tenant separation was still extremely weak, and we were able to demonstrate a different attack vector that also allowed a bypass…” as Wiz put it in a withering May 2022 write-up.
(That issue, now fixed, involved a critical vulnerability in a driver used to connect AWS and Azure data services and exposed “areas in the service where a huge amount of Microsoft and third-party code runs with SYSTEM permissions… on shared machines with access to Azure service keys and sensitive data of other customers.”)
See also: Microsoft mauled over fresh cross-tenant vulnerability
To exploit the Oracle cloud vulnerability, a target “volume” (a virtual disk that provides persistent storage space for compute instances) would have had to be either detached or attached as shareable said Wiz.
“Detached volumes are relatively common because by default the boot volumes associated with terminated compute instances are not deleted. In addition, backup data volumes are often not attached to a running compute instance” the company said in its technical writeup on the vulnerability, which was fixed in July.
The Stack has a number of questions about the bug and will update this piece with more details.
“Insufficient validation of user permissions is a common bug class among cloud service providers. The best way to identify such issues is by performing rigorous code reviews and comprehensive tests for each sensitive API in the development stage,” Wiz noted in its write-up, adding that “Oracle shared with us that it uses static code analysis technology to detect such problems already in development and investigate known and reported issues to ensure the problematic pattern does not recur elsewhere in the codebase. We also recommend performing service-specific penetration tests and participating in bug bounty programs.”
Oracle declined to comment when approached by The Stack.
