Cisco Catalyst SD-WAN controllers are exposed to a maximum CVSS 10 authentication bypass bug that gives attackers the network on a plate.
An APT tracked as UAT-8616 is targeting the vulnerability, allocated CVE-2026-20182, amid ongoing attacks on multiple Cisco SD-WAN bugs.
Vdaemon service targeted: No creds, no certs, no knowledge needed
The authentication bypass bug affects Cisco Catalyst SD-WAN Controller, which has no web UI – specifically the “vdaemon” service, on port 12346.
That’s the DTLS-over-UDP control-plane peering port used by vdaemon for inter-controller and controller-to-edge communication, said Rapid7.
This carries “the entirety of the SD-WAN overlay routing fabric.. compromising this service means compromising the network,” they added.
Cisco Talos says that attacks exploiting this vulnerability are "sophisticated" and so far, limited and targeted. That is likely to change.
Five Cisco SD-WAN vulnerabilities exploited since Feb
The vulnerability is the fifth CVE in Cisco SD-WAN software to be exploited in since February. Cisco Talos has now identified 10 additional threat clusters distinct from UAT-8616 exploiting its SD-WAN proposition.
They're doing everything from dropping cryptominers to infostealers and searching for the admin user’s hashdump, JSON Web Tokens (JWT) used for REST API authentication, and AWS credentials for vManage: AccesKeyId, SecretAccessKey and Token, Talos said late Thursday.
The multiple groups are largely exploiting a chain comprising CVE-2026-20133, CVE-2026-20128, and CVE-2026-20122 since early March 2026, after ZeroZenX Labs published an easy POC exploit.
CVE-2026-20182 is not a patch bypass...
CVE-2026-20182 follows CVE-2026-20127, which is a critical pre-auth RCE in the same component, but the bug is not a patch bypass.
Successful exploitation of CVE-2026-20182 or CVE-2026-20127 provides access to a privileged (non-root) account on the SD-WAN Controller.
That access opens network management protocol NETCONF, letting attackers alter network configuration across the entire SD-WAN fabric, security researchers at Tenable said, adding: “In observed attacks, the threat actor UAT-8616 then leveraged CVE-2022-20775 via a software version downgrade technique to escalate privileges to root.”
Cisco now has patches and indicators of compromise (IoCs) here.
All deployment types are affected
All of its deployment types are affected, ie. on-prem, Cisco SD-WAN Cloud-Pro, Cisco SD-WAN Cloud (Cisco Managed), and Cisco SD-WAN for Government (FedRAMP), it confirmed in its May 14 security advisory.
Rapid7’s Stephen Fewer and Jonah Burgess disclosed CVE-2026-20182 and a POC to Cisco on March 7. Cisco pushed a public security advisory on May 14, over two months later. It was not immediately clear when attacks started.
Rapid7 said: “A remote unauthenticated attacker can bypass authentication by connecting to the vSmart DTLS port with any self-signed client certificate and claiming to be a vHub (type 2) in the CHALLENGE_ACK message… no valid credentials, no CA-signed certificate, and no knowledge of the SD-WAN deployment are required.”
Ports exposed? You're at risk: Cisco
Cisco said of CVE-2026-20182 exploitation:
"Cisco Catalyst SD-WAN Controller systems that are exposed to the internet and that have ports exposed to the internet are at risk of exposure to compromise. In some instances, these indicators of compromises may occur during standard operations. Therefore, they must be assessed against normal network posture to identify and avoid false positives.
"Customers are encouraged to audit the auth.log file, located at /var/log/auth.log, for entries that are related to Accepted publickey for vmanage-admin from unknown or unauthorized IP addresses, as shown in the following example:
2026-02-10T22:51:36+00:00 vm sshd[804]: Accepted publickey for vmanage-admin from port [REDACTED PORT] ssh2: RSA SHA256:[REDACTED KEY]
"Customers must check the IP address in the auth.log log file against the configured System IPs that are listed in the Cisco Catalyst SD-WAN Manager web UI in the WebUI > Devices > System IP column.
"For help determining if a Cisco Catalyst SD-WAN Controller or Cisco Catalyst SD-WAN Manager has been compromised, customers should open a case with the Cisco Technical Assistance Center (TAC). TAC cases should be opened as a Severity 3 with the CVE-ID CVE-2026-20182 in the title.
"Before opening a new TAC case, customers are encouraged to issue the request admin-tech command from each of the control components in the SD-WAN deployment so that the admin-tech file can be provided to the Cisco TAC for review."
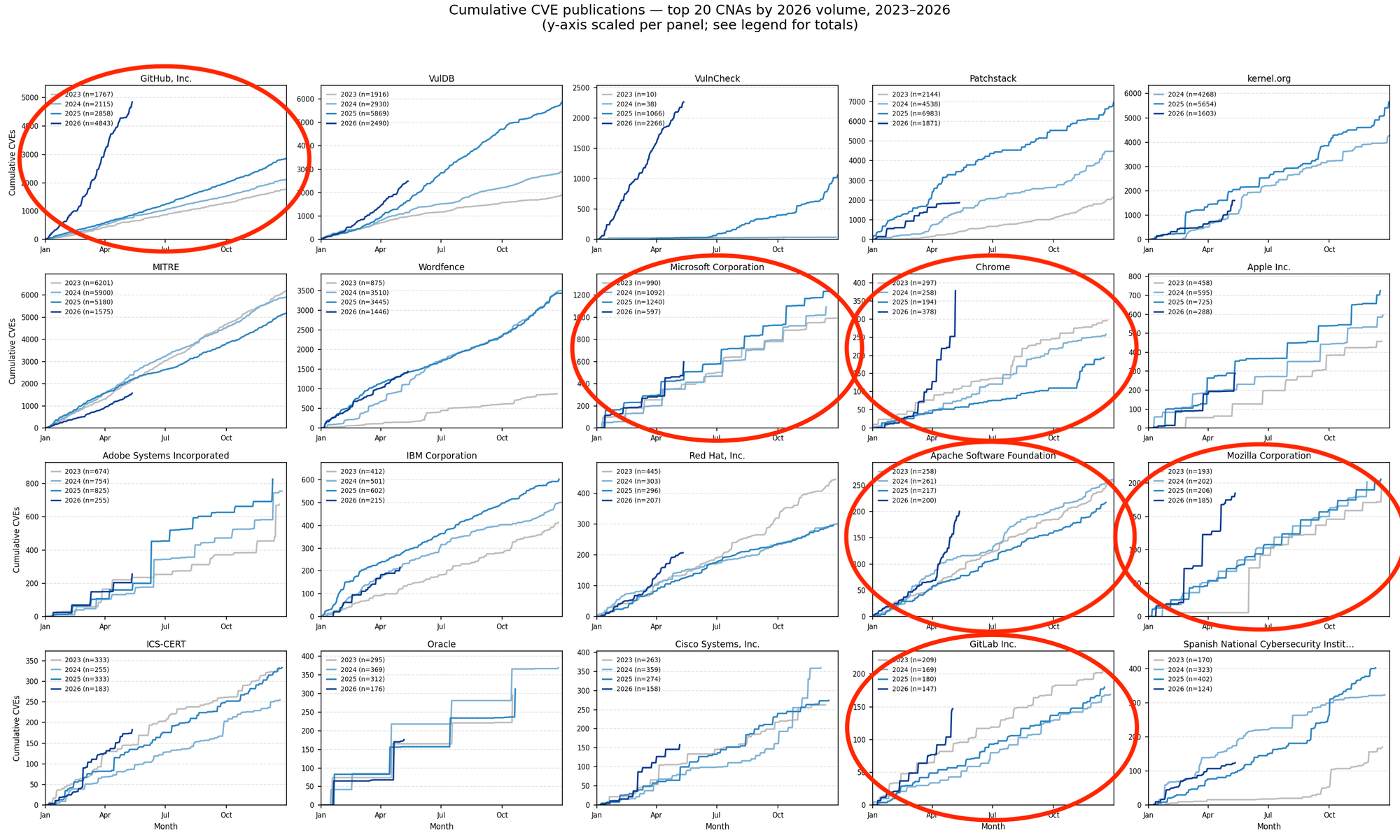
The attacks come as CVE issuance is up sharply year-to-date across several major software suppliers and open-source projects, including Chrome (+563.2%), GitHub (+476.07%), VMware (+180.9%), Apache (+170.3%), Mozilla (+156.9%), HPE (+132.3%), and F5 (+113.8%).
As Vulncheck noted: "While these increases cannot be directly attributed to any single tool or model, the data is consistent with growing speculation that frontier AI models are helping find vulnerabilities that may have previously gone overlooked."
Join The Stack, Intruder and eSentire for a beer and informal conversation about how defenders can react to this surge in zero days in London on May 26, 5pm onwards. Tickets are £20 (£5 for paying members - ask for the code) drinks are on us. All welcome, register below.
 Ed Targett
Ed Targett