cybersecurity
An attacker shift toward black box appliances and lower layers of IT infrastructure has left organisations with a huge security gap

Estonian ex-prez Ilves and Columbia Law prof deliver stark warning to cyberpros

Multiple Fortune 500 firms breached. Threat group uses remote IT staff, social engineering, trojanised npm packages, even a poisoned "tank game"

"Six exploits, no configuration needed, no ports need to get opened; just straight-up RCEs, no fuss, no muss."
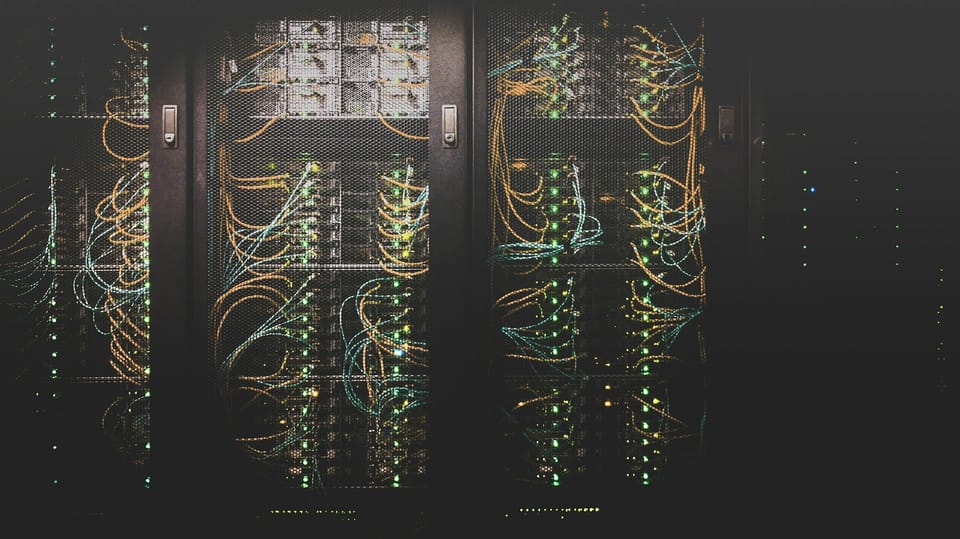
Malware operators “have established a significant presence in data centers worldwide”

18 local authorities along with fire and rescue services to get onboarded to centrally funded Security Operations Centre.


