cybersecurity
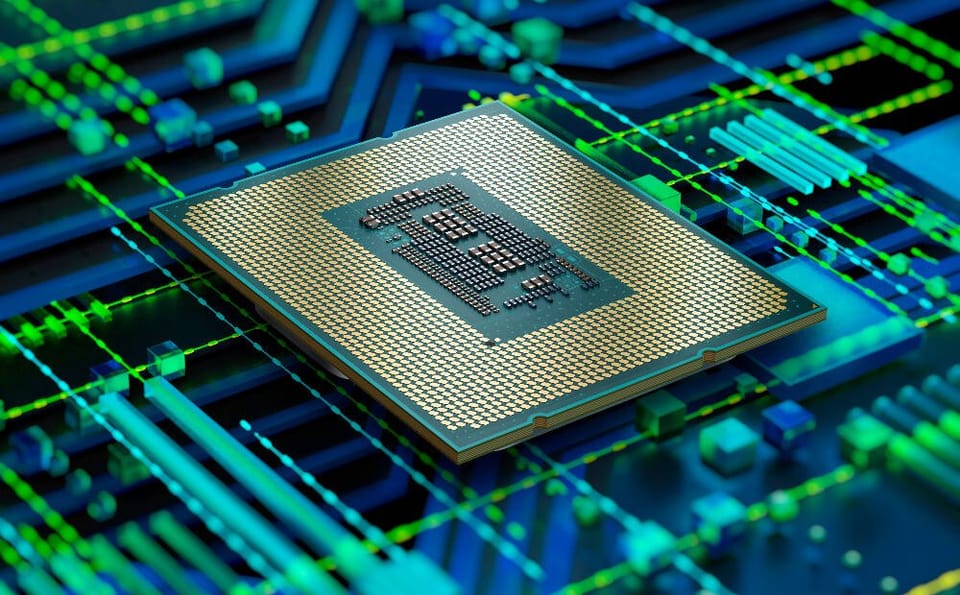
Intel late Sunday confirmed that proprietary UEFI code had been leaked in a potential serious security breach. The Intel Alder Lake source code was leaked to 4chan and Github – as first reported by Tom’s Hardware – as a 6GB file containing sensitive tools and code for building and optimising BIOS/

Absence of a bug bounty programme led to a “race against time” for customer bug bounties...

The British government is changing Companies House name rules to prevent people from creating company names which include code that could sabotage unwary data processors through cross-site scripting (XSS) injection attacks. When a company is registered in the UK, it has to follow certain rules about its name – but provided