Security
"Many CISO may think quantifying risk in business terms is too hard. They will in turn fall back on taken-for-granted 'best practices' like heat maps."

APT deploys web shell disguised as a PNG file in a bid to steal credentials and crack into customers' networks downstream.

"RFPs now look much more thought-out: Cloud security is very much established in most CISOs’ minds as a category.”

Gradio by Hugging Face, Jupyter Server, and Streamlit from Snowflake vulnerable to NTLMv2 hash disclosure of the kind recently exploited by... CISA
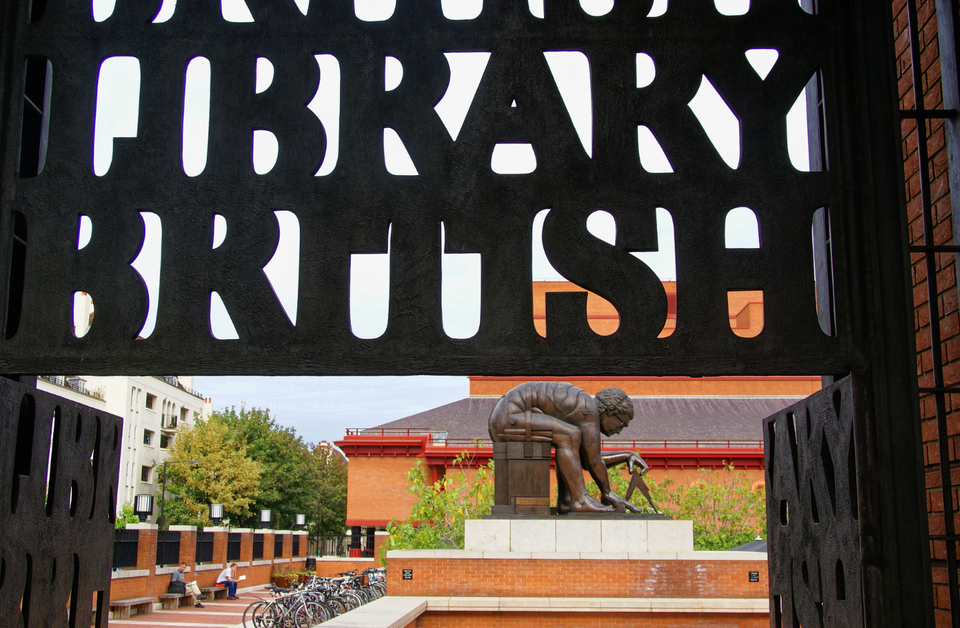
World-famous library is still battling to recover from an incident described as one of the worst in British history.



