Toyota admitted Friday that it had parked the data of millions of drivers – including vehicle location data – on a publicly available cloud database for over a decade owing to human error that went undetected.
As first reported by Reuters, the Toyota data leak affected “2.15 million users in Japan, or almost the entire customer base who signed up for its main cloud service platforms since 2012” as well as Lexus customers.
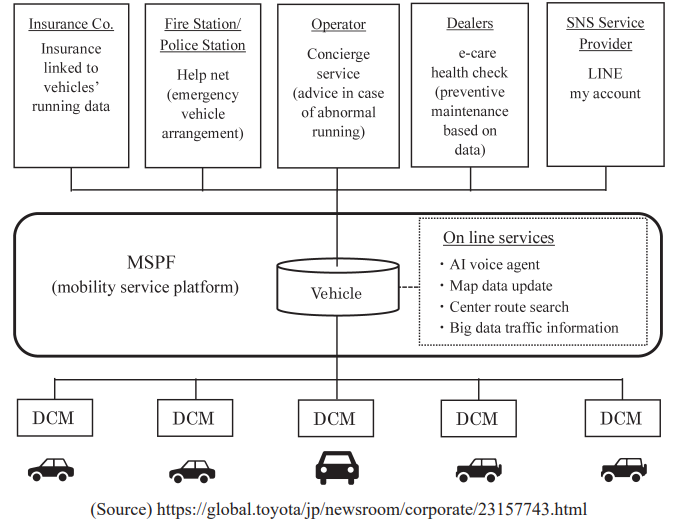
The breach affected customers signed up to Toyota’s T-Connect service which includes AI voice-enabled driving assistance, emergency support in case of traffic accidents and more. Lexus’ G-Link version were also exposed.
(The report did not name the cloud provider in question -- something that is arguably irelevant given the human error component -- but has had a strong relationship with Microsoft Azure since at least 2011, earlier releases show. Public cloud providers continue to tighten up default security settings, with AWS just last month making "block public access" the default for all new S3 buckets created using the S3 API, S3 CLI, the AWS SDKs, or AWS CloudFormation template; it was already the default for the console with the capability first introduced for S3 back in 2017...)
"There was a lack of active detection mechanisms, and activities to detect the presence or absence of things that became public," the spokesperson told Reuters – somewhat obviously – after the Toyota data breach was detected, in response to questions about the astonishing length for which the breach went undetected.
Toyota data breach: Nothing learned from last year?
It is the second major incident to affect Toyota’s T-Connect and customers could be forgiven for expecting better after another critical Toyota data breach detected in 2022 (an incident that took five years to discover…)
The previous T-Connect incident came after a Toyota subcontractor uploaded T-Connect’ source code to a public GitHub repository, including an access key to T-Connect's data server that contained personal information of over 296,000 customers. Toyota apologised for that incident, saying [Google translated from Japanese that] “we once again recognize that the proper handling of customers' personal information is an important social responsibility of a company. We will make further efforts [to improve security].”
See also: Five Eyes kills Russia’s Snake after FSB used weak crypto
Mark Stockley, a senior threat researcher at Malwarebytes said in an emailed comment: “This is a prevalent and increasingly common issue. The wholesale move to The Cloud and "NoSQL" data storage has been accompanied by an avalanche of stories about leaky Amazon S3 buckets, Internet-exposed Elastic Search instances, and unsecured MongoDB databases. Software vendors like Amazon have worked hard to make this kind of thing more difficult, so it isn't as easy as it once was. If a user is determined to expose their data to the Internet, however, they still can, because there are situations where they might actually want to. To avoid accidental exposure, companies can invest in monitoring and auditing of cloud services and settings, as Toyota has said it will. Penetration testing and red team engagements can also help companies identify exposed data”.
It's a good rule of thumb that in any new area of computing, or industry sector that is becoming "smart" or digitally connected, there is a race to see who can get there first, and security is often the first casualty. This is typically followed by a lengthy process of re-learning some hard security lessons. Security problems in the IoT space, which covers everything from million-dollar "smart" farm machinery to connected lightbulbs, are rife - but nothing new. They are broadly just a re-run of what happened on the web 20 years ago.”
He added: “Consumer confidence seems to be remarkably robust in the face of incidents like this…”
The incident was revealed days after Toyota reported annual revenues of 37.154 trillion yen ($275.2 billion), an increase of 18.4% and a figure that suggests it should have ample resources to do a better job of cloud security.
