
The nuclear industry is an attractive target for threat actors ranging from ransomware blackmailers to nation-state actors and even anti-nuclear activists.
But despite the obvious threat, this critical sector "lacks a comprehensive understanding of the threat landscape around cybersecurity" and does not have "effective resilience strategies" in place, a report from the think tank Chatham House has warned.
The independent policy institute said that a growing reliance on nuclear energy in countries across the world has made consideration of cybersecurity risks "more critical than ever." It illustrated this point with a reminder that more than 20 countries including the US, the UK and Canada recently committed to tripling nuclear energy capacity by 2050 to meet net zero targets.
Chatham House also warned that nuclear power plants in warzones such as Ukraine face increased "vulnerability to cyberattacks, as well as physical attacks", whilst the adoption of new technologies such as small modular reactors (SMRs) will increase the likelihood of nuclear facilities "becoming targets in conflict situations". We are already seeing a version of this scenario play out with Russia's attack on Ukraine's Zaporizhzhia plant.
"Expansion of nuclear capabilities brings new challenges, particularly in cybersecurity," Chatham House wrote. "Cyber operations targeting civil nuclear systems have been reported worldwide. Such operations pose significant risks, with potential harms including information theft, equipment malfunction, disruption of energy supplies, environmental damage and health impacts. The risks are prevalent both in peacetime and during conflicts."
In its report, the think tank deals with one of the most pressing questions: could a cyberattack lead to a nuclear meltdown which (we extrapolate) irradiates vast swathes of land and causes death on a terrifying scale?
Thankfully, the answer is something like: "Probably not."
"The impact of a cyber operation targeting civil nuclear infrastructure can be as wide-ranging as the theft of sensitive information, the loss of access to or control over monitoring and control software, operating difficulties, or – in the worst-case scenarios – reactor shutdown or difficulties controlling nuclear storage," the report continued.
"There is only a small possibility that a cyber operation would cause loss of control over a nuclear reactor to the point of meltdown or a significant release of radiation. This is because nuclear power plants have other redundant safety features such as back-ups for cooling.
"However, the potential impacts if a meltdown or major radiation release did occur could be very significant, including deaths or long-term health problems among nuclear power plant workers or members of the public exposed to radiation, as well as long-term environmental damage and contamination."
In cases of a combined cyber and on-ground operation, vulnerabilities in nuclear facilities could be exploited "to overwhelm a limited operating staff, or to create a diversion enabling unauthorised access to nuclear materials."
The report clarifies that this is also an unlikely outcome given the multiple physical safeguards in place at facilities, but there are other tangible damages to physical assets that cybercriminals could use to derail countries and economies.
Communications between plants and operators could be intercepted and impacted, with the potential to disrupt electrical grids. With more countries pivoting to nuclear energy, this is a significant vulnerability.
See also: UK nuclear waste firm Sellafield Ltd. prosecuted over cyber failings
The international affairs think tank isn't the only organisation grappling with cyber threats to nuclear infrastructure. In 2023, the International Atomic Energy Agency (IAEA) held a conference with participants from 94 countries to establish better global cybersecurity protocols for nuclear facilities.
The IAEA projected that nuclear energy capacity will likely double by 2050 to 890 GW(e) compared with today’s 369 GW(e). This is in large part due to countries seeing nuclear energy as a reliable, resilient, and low-carbon energy source in the face of geopolitical upheaval and an uptake in ESG compliance.
However, cybersecurity protocols haven't been able to keep up with this rapid growth. Chatham House analysts noted that a myriad of factors are keeping these measures from evolving as quickly as they should be.
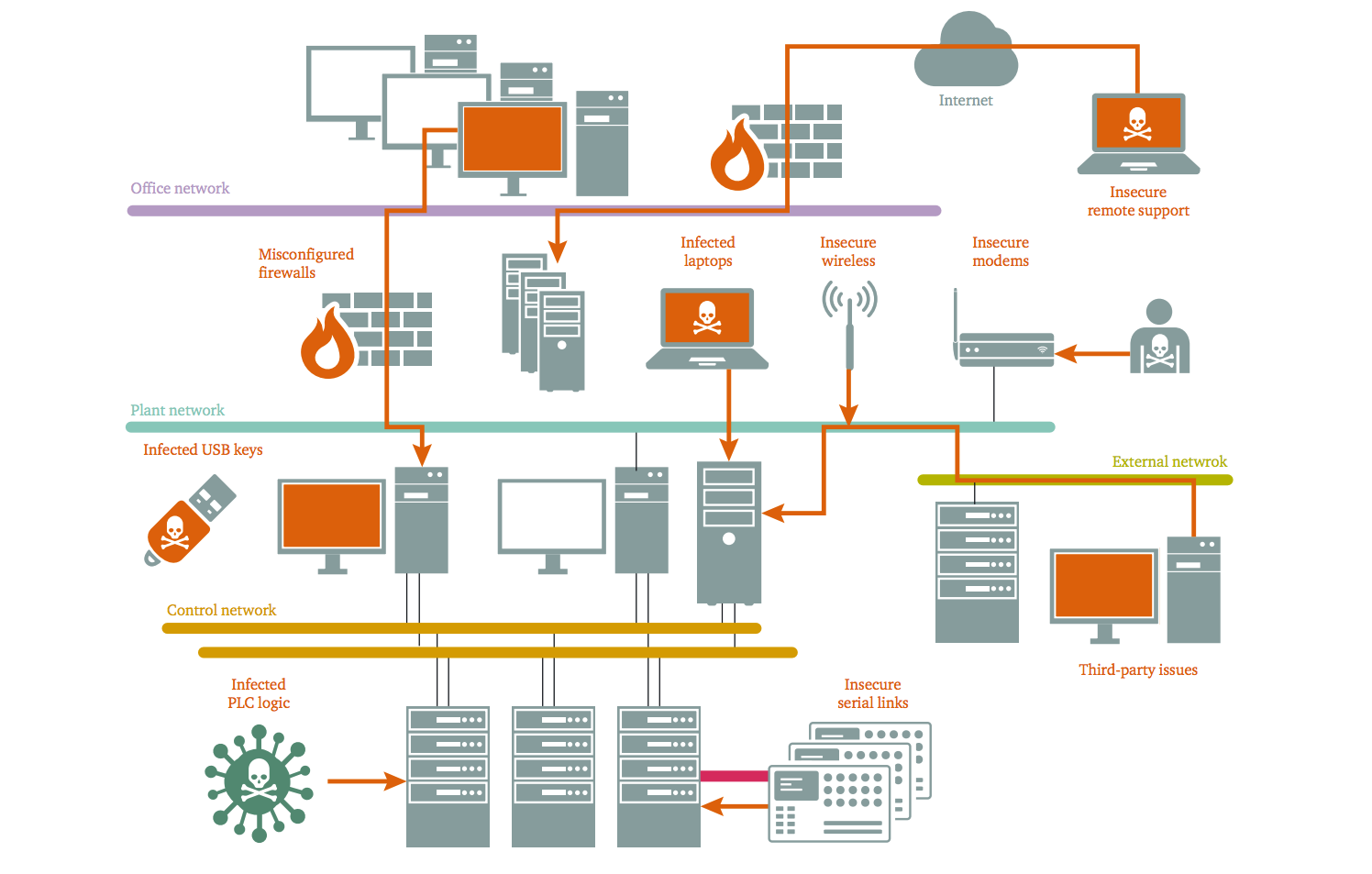
Key cybersecurity vulnerabilities in the civil nuclear sector include the use of older software, the targeting of personnel by threat actors, and the lack of sufficient sector-wide awareness and collaboration on cybersecurity
When it comes to technical vulnerabilities, the nuclear sector is still playing catch-up to other critical national infrastructure when it comes to modernising its IT measures.
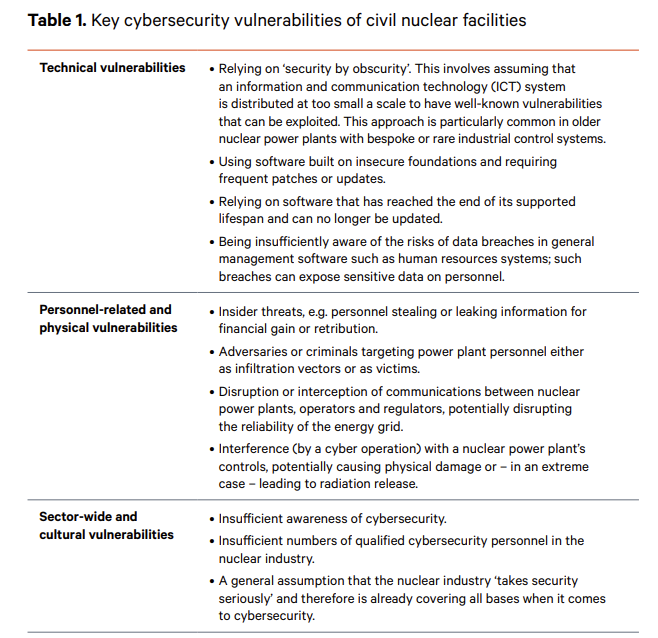
The isolated regulatory environment governing nuclear facilities means that there is no exchange of best practices, and knowledge pathways for security leaders in the sector are ad hoc. The report also notes that the sector lets perception get in the way of transparency, meaning there is little publicly available information about cybersecurity incidents.
The analysts recommend that disclosures would bolster confidence in working practices.
Additionally, the analysts highlighted the difficulty governments face in enforcing cybersecurity standards because most nuclear energy installations are privately run. As AI makes launching cyberattacks even easier, the general increase in risk levels will also impact the nuclear sector.
However, newer reactors are better designed in regards to cyberthreats, though exact levels of security vary from country to country. Largely, the analysts conclude, the threat landscape in the civil nuclear sector is quite mixed .
A number of comprehensive guidelines are available to make nuclear reactors more cyber-secure. If attacks on critical national infrastructure worsen, countries are likely to take these more seriously.