Updated 10:30am GMT, March 4, 2021 with further details from Qualys.
Cybersecurity firm Qualys says it is "aware [of] and investigating" a data breach, after corporate documents belonging to the company were posted to a dark web site. The company late Wednesday March 3 confirmed the data was stolen after a zero day in Accellion’s legacy File Transfer Appliance (FTA) was abused by hackers in December 2020 to steal data from a range of Accellion FTA users. (The managed third-party service was used by Qualys to transfer files to customers.)
Data posted on an onion site as seen by The Stack, showed a range of commercial documents dated between 2016 and late 2020, including contract terms with a Japanese customer and a security report summary for a multinational professional services firm that, worryingly, reveals vulnerabilities in the latter's infrastructure. (While widely reported as a ransomware attack, it would be better described as extortion. No Qualys systems themselves were compromised, codebases affected, or computers/networks locked.)
Qualys CISO Ben Carr said: "Qualys has confirmed that there is no impact on the Qualys production environments, codebase or customer data hosted on the Qualys Cloud Platform. All Qualys platforms continue to be fully functional and at no time was there any operational impact."
Companies impacted by the leak of Qualys customer data had been notified after initial investigations revealed Qualys' exposure to the Accellion breach, it said.
The following CVEs have been allocated to the recent Accellion breaches (see more here from FireEye Mandiant):
- CVE-2021-27101 - SQL injection via a crafted Host header
- CVE-2021-27102 - OS command execution via a local web service call
- CVE-2021-27103 - SSRF via a crafted POST request
- CVE-2021-27104 - OS command execution via a crafted POST request
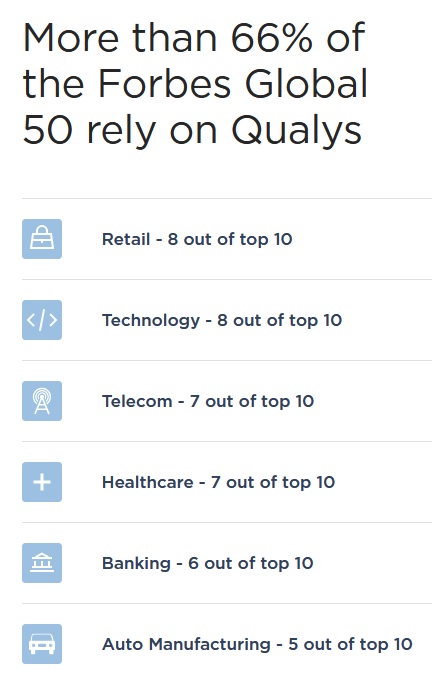
The incident -- widely misreported as a compromise of Qualys' systems -- left customers sweating: its security tools are deployed in managed security services from Deloitte, Infosys, and other partners.
Numerous security vendors have fallen victim to hackers this year alone: the incident follows a major compromise of FireEye. Microsoft has admitted that a 0day in its Microsoft Defender security product was actively exploited in the wild; Malwarebytes suffered a breach of an O365 tenant, with Mimecast also admitting a breach.
The ransomware associated with this particular group of threat actors has typically been dropped via spear phishing campaigns, SMB exploits, and compromised AD administrator credentials in the past, particularly by the TA505 threat group, who security experts say typically focus on "big game hunting" (carefully focussed attacks on large targets). Recent victims include aerospace firm Bombardier.
South Korea's S2W LAB has a detailed write-up on TTPs for the group here. Qualys has hired FireEye Mandiant to help investigate. While the incident is less severe than many pundits had speculated ("19,000 Qualys customers at risk" shrieked one security site wrongly in a now-deleted Tweet"), Qualys will no-doubt be assessing its supply chain carefully: Accellion FTA is a legacy product nearly 20 years old and close to EOL. Alternatives are available.
