
A former NSA IT staffer has been sentenced to 21 years for espionage after attempting to sell classified documents to Russia for $85,000.
Jareh Sebastian Dalke, 32, served as a Information Systems Security Designer for the NSA for a month between June and July 2022.
He abruptly tendered his resignation on June 28, 2022.
See also: OpenAI, TikTok, X hunt insider threat specialists – on widely diverging salary bands
He subsequently shared Top Secret files over an encrypted email with a contact whom he thought was a Russian spy – he was mistaken.
Among them were a 14-page document about NSA “plans to update a certain cryptographic program” a court document showed.
“This defendant, who had sworn an oath to defend our country, believed he was selling classified national security information to a Russian agent, when in fact, he was outing himself to the FBI,” Attorney General Merrick Garland said in a press release about the sentencing, published April 29.
NSA insider attempted to sell Russian
Dalke had pleaded guilty in 2023 to six charges of attempting to transmit classified National Defense Information to a Russian agent.
He had told the FBI agent that he applied for his NSA position because he had “questioned our role in damage to the world in the past and by mixture of curiosity for secrets and a desire to cause change.”
The condensed time frame between him resigning and his interactions with the FBI suggest that either his document access or abrupt departure had raised red flags in the agency – which has grappled with insider risk.
See also: NASA warned over IT insider risk
His prosecution follows the leak of NSA secrets by Edward Snowden and Reality Winner; more recently, a junior sysadmin, Jack Teixeira, faced court after using his access to the sensitive Joint Worldwide Intelligence Communications System (JWICS) to download confidential documents.
That latter incident raised fresh concern in US security circles about the number of comparatively junior people with Top Secret clearance; believed to be as high as the five-figure range.
“There’s the obvious question of why someone in this relatively low rank and rather obscure corner of the military, namely the Massachusetts Air National Guard, could have access to not only some of the nation’s most critical secrets, but such an extraordinary array of them, which could have no possible bearing on his job,” said Glenn Gerstell, a former NSA general counsel, at the time.
Dalke pleaded guilty in court in 2023 to six counts of attempting to transmit classified NDI to a foreign agent. This week he was charged with Espionage and sentenced to 263 months in prison.
“This sentence demonstrates that those who seek to betray our country will be held accountable for their crimes,” Garland added.
The Department for Homeland Security commented late 2023, “Increasingly, insider threat cases and high-profile data leaks illustrate the need for strong insider threat programs within organisations.”
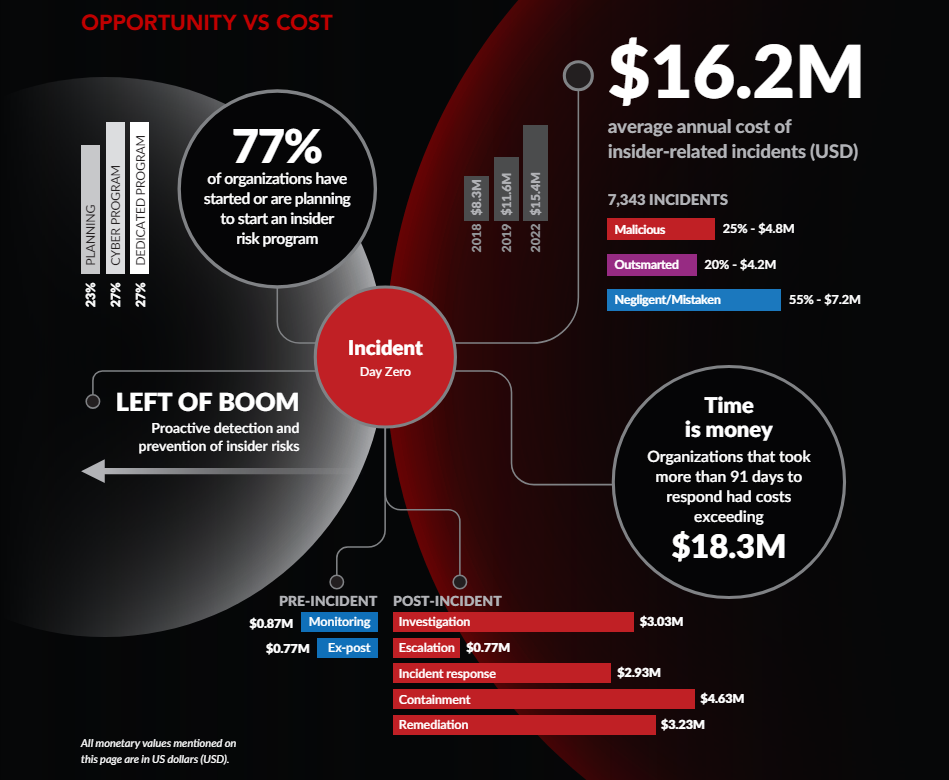
Analysis suggests that insider threat security incidents are increasing. The Ponemon Institute and DTEX's 2023 insider risks report. That report found that 71% of companies are experiencing between 21 and 40 insider incidents per year. Whilst the majority of these are negligence-related, some 25% of incidents are malicious, it found. The US’s Cybersecurity and Infrastructure Security Agency provides an insider threat mitigation guide with some step-by-step framework principles for anyone looking, here.
