
Exploitation of one Citrix vulnerability triggered “13 separate nationally significant incidents” in 2023 that required the intervention of the UK’s National Cyber Security Centre, according to the agency’s annual report.
This was not “Citrix Bleed” (CVE-2023-4966) another widely exploited Citrix vulnerability this year, which has gained more attention, but rather CVE-2023-3519, disclosed by the vendor in an advisory on July 18, 2023.
The Citrix vulnerability that forced urgent intervention by security services professionals, CVE-2023-3519, was first exploited as a zero day in June and used to attack critical national infrastructure (CNI) in the US.
Don't miss out: Follow The Stack on LinkedIn
It has a critical CVSS rating of 9.8 and is a pre-authentication remote code execution bug that gives an attacker root access to Citrix gateways.
This kind of incident and threat landscape means that “we need to continue improving our aperture on CNI (Critical National Infrastructure) risk,” the NCSC noted: “For example, it will be key to understand flaws in the design of the UK’s CNI (such as inadequate network segregation).”
It may also be “necessary to expand threat hunting for nation states who could seek to pre-position on UK CNI” the agency warned industry partners, hinting strongly at a more interventionist approach in future.
The NCSC said: “The highest proportion of incidents handled by the NCSC resulted from the exploitation of applications… to aid the prevention of incidents such as this, caused by poor cyber hygiene, the NCSC sent over 16,000 notifications of vulnerable services via our Early Warning Service.”
Cyber hygiene? Well yes; upstream too please
Whilst the NCSC is right to flag poor cyber hygiene (those hit will have included those who didn’t patch) the vendor here also deserves attention, not least because the root cause is a basic buffer overflow.
This vulnerability in particular was also exploited as a zero day *before* a patch was made available. (The NCSC did not specify whether the attacks in the UK came before or after Citrix issued a patch for the vulnerability.)
And as security firm Bishop Fox noted, analysing the vulnerability in July “the complete lack of exploit mitigations made this vulnerability extremely easy to exploit on VPX builds [Citrix/NetScaler’s form factor to run the gateway on a hypervisor]. For comparison, we were unable to exploit the CPX (containerized) builds of nsppe due to presence of a stack canary immediately following the buffer that we were overflowing.
CVE-2023-3519: Tell me more?
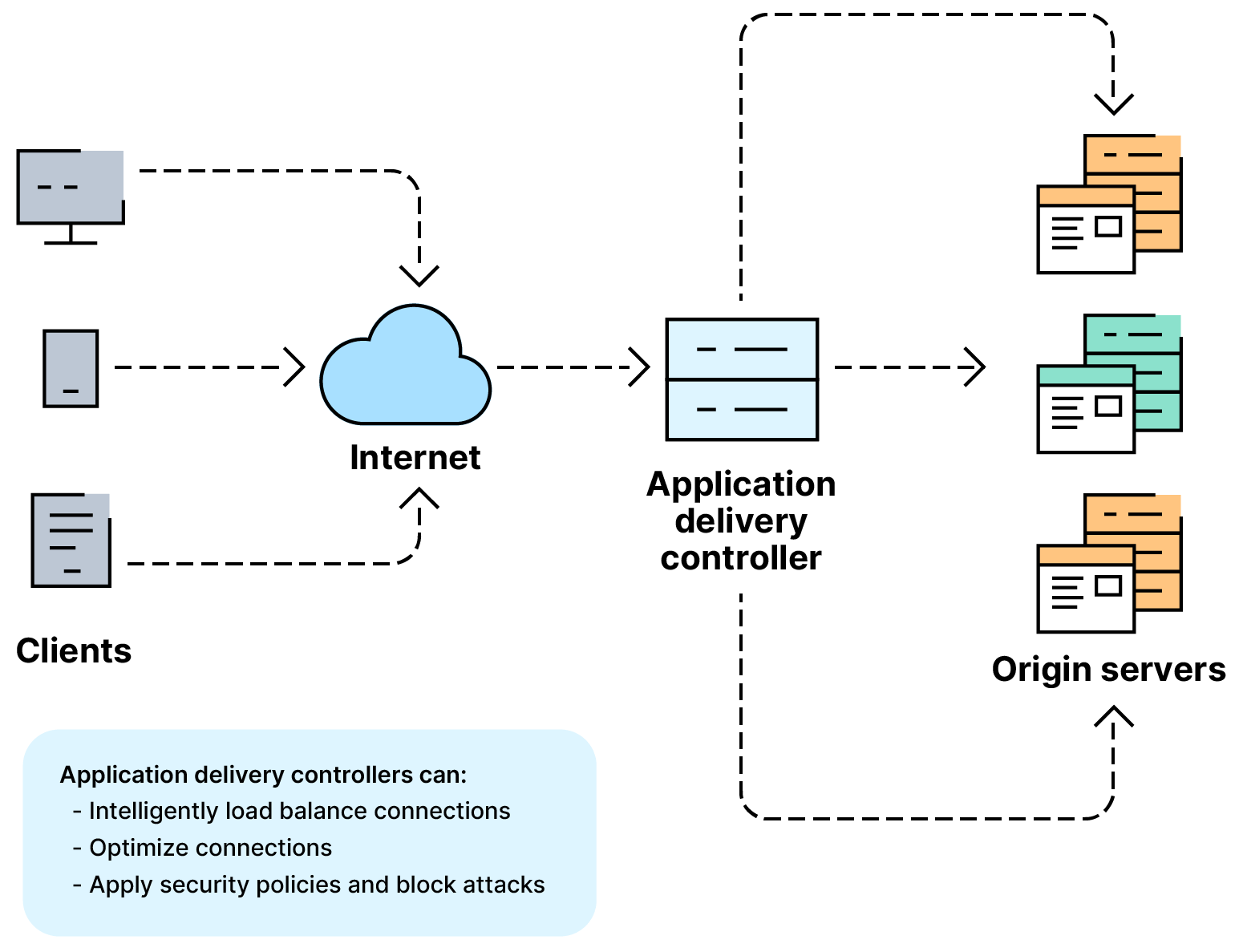
The bug affects the following versions of NetScaler ADC (formerly Citrix ADC) and NetScaler Gateway (formerly Citrix Gateway).
- NetScaler ADC and NetScaler Gateway 13.1 before 13.1-49.13
- NetScaler ADC and NetScaler Gateway 13.0 before 13.0-91.13
- NetScaler ADC 13.1-FIPS before 13.1-37.159
- NetScaler ADC 12.1-FIPS before 12.1-55.297
- NetScaler ADC 12.1-NDcPP before 12.1-55.297
Rapid7 has an AttackerKB article; here's a blog post by Assetnote; here's a writeup by Bishop Fox;
The company’s security team noted: “This follows the trend of missing exploit mitigations that we have observed in many networking appliances, including but not limited to PAN-OS and FortiGate. We hope that vendors will take note of the importance of enabling basic compile-time exploit mitigations, as they can make exploitation of many common bugs difficult or impossible while imposing minimal performance penalties…”
An email from The Stack to Citrix's press office email as listed on its website bounced back, saying that email did not exist.
As The Stack noted in July, despite apparently knowing of the vulnerability and exploitation in the wild in June, Citrix did not publish any emergency mitigations until the following month when it had a patch ready.
The US CNI attack was thwarted by a strong security posture. As the US’s NCSC counterpart, CISA, noted on July 21, in that incident after landing a foothold “the actors attempted to move laterally to a domain controller but network-segmentation controls for the appliance blocked movement.”
The attackers then used a key stored on the vulnerable NetScaler ADC to decrypt Active Directory (AD) credentials that they then used to authenticate with the DC from the ADC via a virtual machine; But “firewall and account restrictions (only certain internal accounts could authenticate to the DC [domain controller]) blocked this activity.” CISA said on July 20.
Somebody give that CISO and their team a pay rise.
