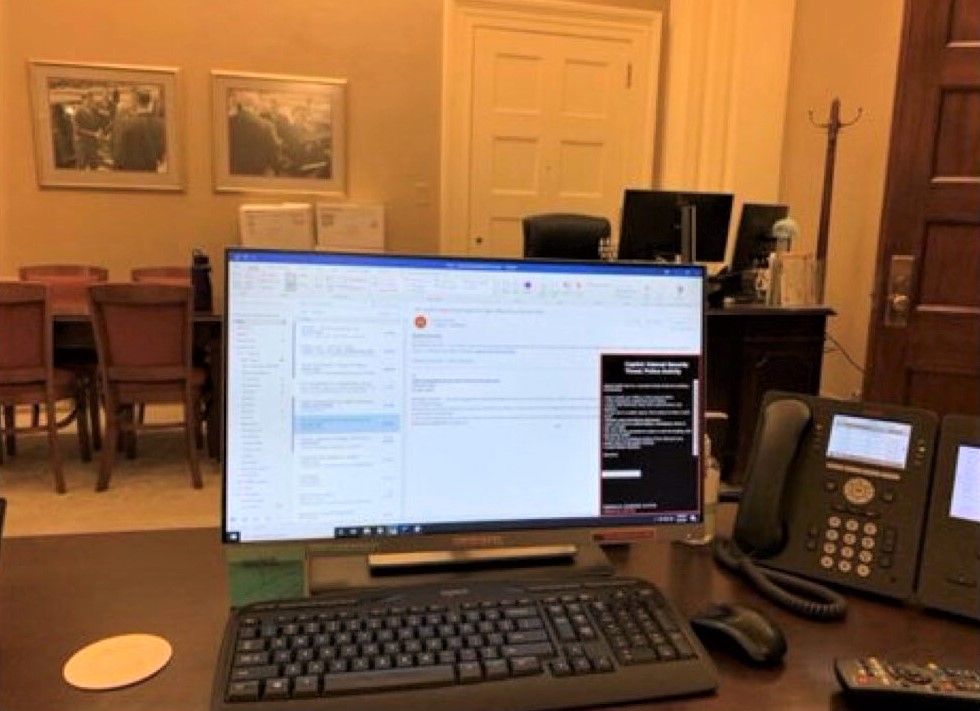
Cybersecurity experts say Wednesday's mob entry to Congress offices represents a serious threat to the integrity of US federal IT networks, after individuals who broke in were photographed next to seemingly unlocked computers -- including that of Speaker Nancy Pelosi. (Pictured).
Physical access to machines and offices is mecca for those with bad intentions. In theory the chaos could have been used to plant malware on open machines, steal and rifle through hardware, or even hide devices that could facilitate man-in-the-middle (MITM) attacks.
This would not necessarily have to have been done by pro-Trump agitators, but those using the incident for operational cover.
As one security researcher put it: "If you don’t think there are foreign agenda in that crowd — who now have unfettered, unrecorded, and unrestricted access — you are naive. The security of the United States is deeply, deeply compromised. One presumes agents have been inside the building for hours. Assume SCIFs breached. Assume malware planted in all systems. Assume all computers compromised. Assume bugs installed. Assume all networks compromised, including private RF networks."
The House CISO oversees a $21 million annual cybersecurity budget, runs a sizeable security team and has a 24x7 full time Security Operations Center. But as one former Congress sysadmin put it on Twitter (The Stack separately confirmed their identity): "Knowing House IT stuff, I don't think I'd sleep well until the networks were rebuilt from scratch and every computer wiped and the internals visually inspected before being put back in service. Every printer, every copier. Every nook and cranny.
https://twitter.com/alizaslav/status/1347033165764972551
He added: "[I'm] not worried about the MAGA types so much as nation-state operators, or private-sector operators, taking advantage of the chaos to slip in with a good kit and try and leave some persistent access routes."
As Congressional leaders and aides were scrambled out of the Chamber and offices by security, many appear to have left computers open and unattended. Video imagery from the seen shows ransacked offices.
Experts say inventory checks will be an early priority, one corporate network security expert told The Stack (declining to be named as their company hadn't cleared them for comment): "It genuinely is an IT security nightmare, and will not be a small job to fix" they said, adding: "The first port of call will be to count inventory. At this point, we have no idea how many devices were on the premises or if any have been removed.
"All user account activity must be investigated from the time of evacuation. All assets, user accounts, and files will need to be inspected and monitored in case of nefarious activity. Even if not directly, the chaos in the Capitol will have provided the perfect cover for malicious actors to organise one or more cyberattacks. Ultimately it only takes one person to have accessed one asset for there to be a serious issue. Ongoing meticulous vigilance is vital - both in terms of compromised machines and how physical and cybersecurity is being addressed at the Capitol.”
