
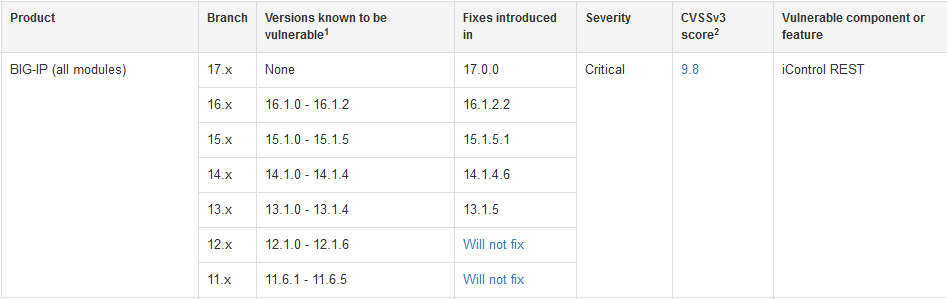
A critical vulnerability in F5's BIG-IP software (CVE 2020-5902) was among the top ten software flaws most exploited by hackers in 2020. Now a new BIG-IP vulnerability (CVE-2022-1388) in the load balancing and security suite gives an unauthenticated attacker remote code execution (CVSS 9.8). Users should patch urgently.
The vulnerability was found internally and has not yet been reported as publicly exploited. But a proof-of-concept (POC) exploit is likely to follow shortly as offensive security professionals reverse engineer the patch.
https://twitter.com/pedrib1337/status/1523629083585695744
UPDATED May 9: Public exploits galore followed, as predicted, within days. Those that configured F5 box as a load balancer and firewall via self IP also appear to be vulnerable, with thousands still exposed. There is effectively no authentication needed for the /mgmt/tm/util/bash endpoint
As with 2021's (also exploited) fellow CVSS 9.8 BIG-IP vulnerability (CVE-2021-22986) the new BIG-IP vulnerability lies in its iControl REST API, which is designed to provide “granular control” over its configuration.
There appears to be some 16,000 BIG-IP systems with a management interface on the public internet according to Shodan and Censys searches. Amazon, Google Cloud, Huawei, Microsoft, Korea Telecom and countless other telcos were among those seemingly exposed according to a Censys search by The Stack. (Clearly some of these may be honeypots. Others will just be nectar for hackers. F5 has extensive mitigation guidance available here.)
The simplest and most sensible mitigation is to block iControl REST access through the management interface/restrict management access only to trusted users and devices over a secure network.
Those for reasons of their own unable to do this can also block all access to the iControl REST interface of their BIG-IP system through self IP addresses. As F5 guides users: "Change the Port Lockdown setting to Allow None for each self IP address in the system. If you must open any ports, you should use the Allow Custom option, taking care to disallow access to iControl REST. By default, iControl REST listens on TCP port 443 or TCP port 8443 on single NIC BIG-IP VE instances. If you modified the default port, ensure that you disallow access to the alternate port you configured." (Be warned: the company adds that performing this latter action "prevents all access to the Configuration utility and iControl REST using the self IP address. These changes may also impact other services, including breaking high availability (HA) configurations...")
A 2021 report by WhiteHat Security found that the average time taken to fix critical cybersecurity vulnerabilities was 205 days. There are often technical or organisational hurdles standing in the way of patching (e.g. enforcing a patching window for critical systems, especially if they’re legacy infrastructure) and dependencies that mean a patch will bring a critical system to a halt. Most security teams also have far more vulnerabilities to patch than time and resources to patch them. Business leaders should be mindful that resourcing a security team or just IT more broadly is likely to be a lot cheaper than remediating a ransomware attack -- this week's news from freight forwarder Expeditors that remediation after a February attack had cost it $20 million in IT remediation and incident response consultants and $40 million more in lost earnings is a clear case in point.
