
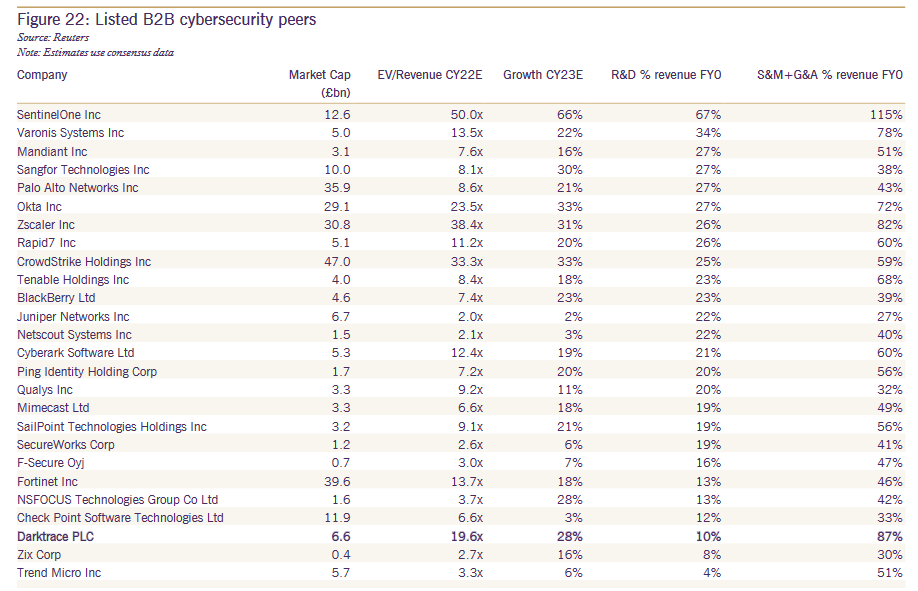
Shares in British cybersecurity company Darktrace tumbled 24% early this week after broker-dealer Peel Hunt warned that the vendor could be worth 50% less than its current valuation in an excoriating report, which pointed to the company's low R&D spend (the third lowest among 26 peers) and highlighted criticisms from customers over its AI claims, saying "many felt it was more of a glorified rule/pattern-based system."
Darktrace floated on the London Stock Exchange (LSE) in April 2021 at 250p a share. As The Stack published they were trading at 728p, down from Friday highs of 965p. Darktrace's growth has been "driven by its powerful go-to-market strategy," Peel Hunt's analysts said, adding: "Having considered the potential market size, the intensifying competition, and Darktrace’s limited R&D spend, we take a more grounded approach to our valuation, giving a target price of 473p". (Darktrace had not responded to a request for comment as we published.)
Peel Hunt added that "Darktrace’s price also makes it harder to justify in a budget review once the product is already bought. Not only is it expensive, but it also more of a general-purpose security product compared to others, meaning the ramifications of eliminating it are less obvious and making it harder to argue to keep it."
"Ultimately, as technologists, we are not 100% convinced that being first to market and having great sales and support is enough to build long-term value" Peel Hunt's analysts wrote in a report seen by The Stack.
See also: 7 free enterprise-ready cybersecurity tools
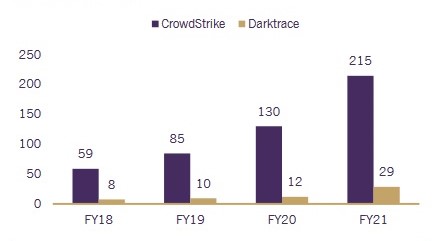
Darktrace spent 82% of revenue on sales and marketing last year, and 6% on research and development, the Economist noted in April. It has nonetheless been generating strong results, with on October 13 trading update (for its 2022 Q1, or the quarter ending September 30, 2021) pointing to revenues of $93.1 million, up 50.8% over the same quarter of FY 2021. The company now says it has 5,975 customers, up 42.7% year-on-year.
Rivals say the company's anomaly-based system "only finds what is different, not malicious" and, as one commentator in a /sysadmin thread on its products notes it's "sort of a SIEM, but not really.... sort of a network monitoring tool, but you still need one of those. [It's email protection service] Antigena is sort of EDR, but you still need something on the endpoint..."
Read this: Veeam's CISO on life as a cop, reporting to the board, and sleeping well at night with a target on your back
Choosing cybersecurity solutions remains a challenging task for most. HMG estimates that there are 1,221 firms active within the UK providing cyber security products and services (2019) alone with tens of thousands more globally and it's tough for CISOs or CIOs to look "under the hood" of many products in any meaningful way given often complex setup requirements, opaque "AI" models and the flurry of false positives many generate.
Executives choosing endpoint protection platforms in particular (and not relying solely on trusted partners, many of which do robust testing: we've spoken to CGI in the past, for example, on how it approaches this and been impressed) can do worse than start by checking performance in MITRE Engenuity ATT&CK testing.
(See for example this 2021 MITRE Engenuity ATT&CK battery of tests that checked vendors' ability to identify attacks that mimicked the tactics of Carbanak , a threat group that mainly targets banks, and FIN7, a threat group that has primarily targeted the retail, restaurant, and hospitality sectors.)
