
Four draft cyber insurance contract clauses published by Lloyd’s Market Association (LMA) – a membership network for the influential insurance marketplace – suggest that organisations look ever more closely at their policies as premiums soar and the LMA moves to ensure every contract has a broad cyber-war exclusion.
The LMA, whose member agencies underwrite approximately £36 billion each year, November 25 published four alternative clauses to include in standalone cyber-insurance contracts. These have been drafted to meet Lloyd’s requirements, set out in July 2020, which state that “all insurance and reinsurance policies written at Lloyd’s must, except in very limited circumstances, contain a clause which excludes all losses caused by war”
The different clauses have been "drafted to provide Lloyd’s syndicates and their (re)insureds (and brokers) with options in respect of the level of cover provided for cyber operations between states which are not excluded by the definition of war, cyber war or cyber operations which have a major detrimental impact on a state” the LMA said, noting that underwriters should closely “consider the coverage provided, their outwards reinsurance wording and the resultant impact on exposures across the portfolio” when choosing which clause to use.
See also: Want to hire a CISO? Know this...
The clauses offer subtly different approaches to how insurers cover cyber war exclusion.
One, for example, notes that a policy does not cover “any loss, damage, liability, cost or expense of any kind (together “loss”) directly or indirectly, occasioned by, happening through or in consequence of:
"1.1. war or a cyber operation that is carried out in the course of war; and/or 1.2. retaliatory cyber operations between any specified states leading to two or more specified states becoming impacted states; and/or 1.3. a cyber operation that has a major detrimental impact on: 1.3.1. the functioning of a state due to the direct or indirect effect of the cyber operation on the availability, integrity or delivery of an essential service…
One of the clauses explicitly ensures “paragraph 1.3 shall not apply to the direct or indirect effect of a cyber operation on a bystanding cyber asset” – suggesting that other policies may not cover collateral damage of an APT campaign. (It defines “bystanding cyber asset” as a “computer system used by the insured or its third party service providers that is not physically located in an impacted state but is affected by a cyber operation.”)
Cyber insurance war exclusion: Who says it’s “war?”
So who determines if a cyber attack constitutes war or not? (War is very loosely defined; more on that below).
“The primary but not exclusive [our italics] factor in determining attribution of a cyber operation shall be whether the government of the state (including its intelligence and security services) in which the computer system affected by the cyber operation is physically located attributes the cyber operation to another state or those acting on its behalf” the draft clauses note. They define “war” meanwhile broadly not just as (14.1) “the use of physical force by a state against another state or as part of a civil war, rebellion, revolution, insurrection” but also more broadly (14.2) as “military or usurped power or confiscation or nationalisation or requisition or destruction of or damage to property by or under the order of any government or public or local authority.” (UK residents, consider this next time your local authority wields a compulsory purchase order on some land for development...)
Commenting on the clauses, Matt Middleton-Leal, Managing Director EMEA North, at cybersecurity firm Qualys, noted to The Stack: “Looking at the Lloyds material on cyber insurance, some of the guide policies include protection for ‘bystander attacks’ and some do not. Bystander attacks are a risk where a specific nation state attack affects IT systems used by other companies that have the same applications or IT set-ups in place, and they get hit in the blast radius. While they are not the specific target they may get hit in the same way.
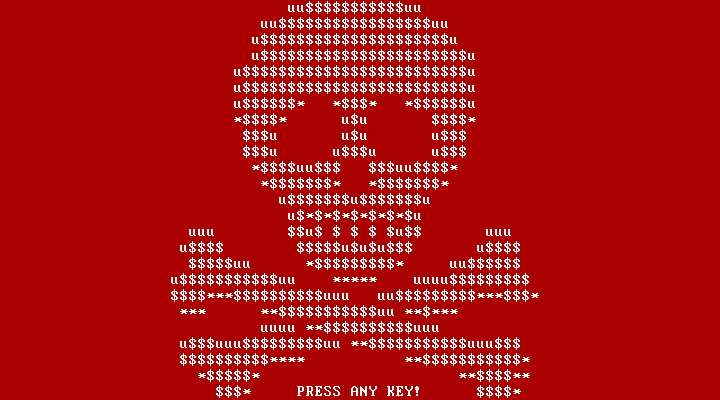
“Petya in 2017 is a good example of this - the attack was aimed at Ukrainian companies, but other companies around the world were affected” he noted, adding: “With policies getting more stringent, company leadership teams will have to think harder about their IT strategies and invest in more baseline security programmes rather than relying on their insurance to manage risk for them.
"Organisations will have to be a lot more assiduous in their planning in order to get support if they do carry on with their policies. In 2022, we’ll see insurers start to mandate basic security hygiene before they agree to cover any organisation. “Premiums will rise further”, he suggested, adding that “many organisations will look to secure themselves in house, rather than paying for an external provider that may or may not cover them.”
Middleton-Leal wrote as cyber insurance premiums for industries hardest hit by cybercrime soared as much as 300% at renewal. That’s according to Risk Placement Services Inc., a unit of Arthur J. Gallagher & Co., in a report on October 5. Companies and organisations in education, government, health care, construction and manufacturing are among those bearing the brunt of those price increases, the US report said.
Lloyd's of London, which has around a fifth of the global cyber market, has discouraged its 100-odd syndicate members from taking on cyber business next year, industry sources told Reuters on condition of anonymity this month. “Insurers are changing their appetites, limits, coverage and pricing,” Caspar Stops, head of cyber at insurance company Optio told the wire agency this month, adding: “Limits have halved – where people were offering £10 million ($13.50 million), nearly everyone has reduced to five.”
Risk Placement Services Inc. saw even lower risk appetite: "Insurers that were more than eager to issue $5 million cyber liability policies last year have scaled back to limits of $1-3 million in 2021, even on renewals", it noted in its October report: "As a result, building a cyber liability coverage tower has become more challenging."
