Updated June 6 with CVE, details on checking for compromise in MOVEit Transfer, Microsoft attribution and more.
A critical SQL injection vulnerability in Progress Software’s MOVEit Transfer software is under active attack by a growing number of threat actors. Customers should patch or mitigate with extreme urgency.
The MOVEit Transfer vulnerability as first publicly disclosed by Progress Software on May 31. Security researchers at Rapid7 said June 1 that there were seeing automated exploitation of the vulnerability with the same webshell name being dropped in multiple customer environments.
As The Stack published the vulnerability had not been allocated a CVE. UPDATED June 5. This has now been allocated CVE-2023-34362.
Security researcher Kevin Beaumont, typically a reliable source, said that there are now "a double digit number of orgs who had data stolen, that includes multiple US Government and banking orgs."
Microsoft is attributing the attacks to group it dubs Lace Tempest, known for ransomware operations and running the Clop extortion site. Redmond added in a June 4 blog that "depending on the database engine being used (MySQL, Microsoft SQL Server, or Azure SQL), an attacker may be able to infer information about the structure and contents of the database in addition to executing SQL statements that alter or delete database elements..."
Progress Software is advising MOVEit customers to check for indicators of unauthorised access over “at least the past 30 days,” which implies that attacker activity was detected before the vulnerability was disclosed.
How can I check for exploitation?
MOVEit writes its own Windows EVTX file, which is located at C:\Windows\System32\winevt\Logs\MOVEit.evtx. The MOVEit event logs contain a single event ID (Event ID 0) that provides a plethora of information, notes Rapid7, including the following:
- File name
- File path
- File size
- IP address
- Username that performed download
While event logging is not enabled by default in MOVEit Transfer, it's common for their customers to enable it post-installation. Many should have records available on the host. Affected organizations and incident responders can run a report that return alls File Download actions from the audit log from the months of May and June of this year, with all associated fields. The ‘Fields’ value could then easily be limited to just the relevant data from that point. NOTE: It is critical that MOVEit customers capture this log data before wiping or restoring the application from an earlier backup.
Progress has provided a file with IOCs here.
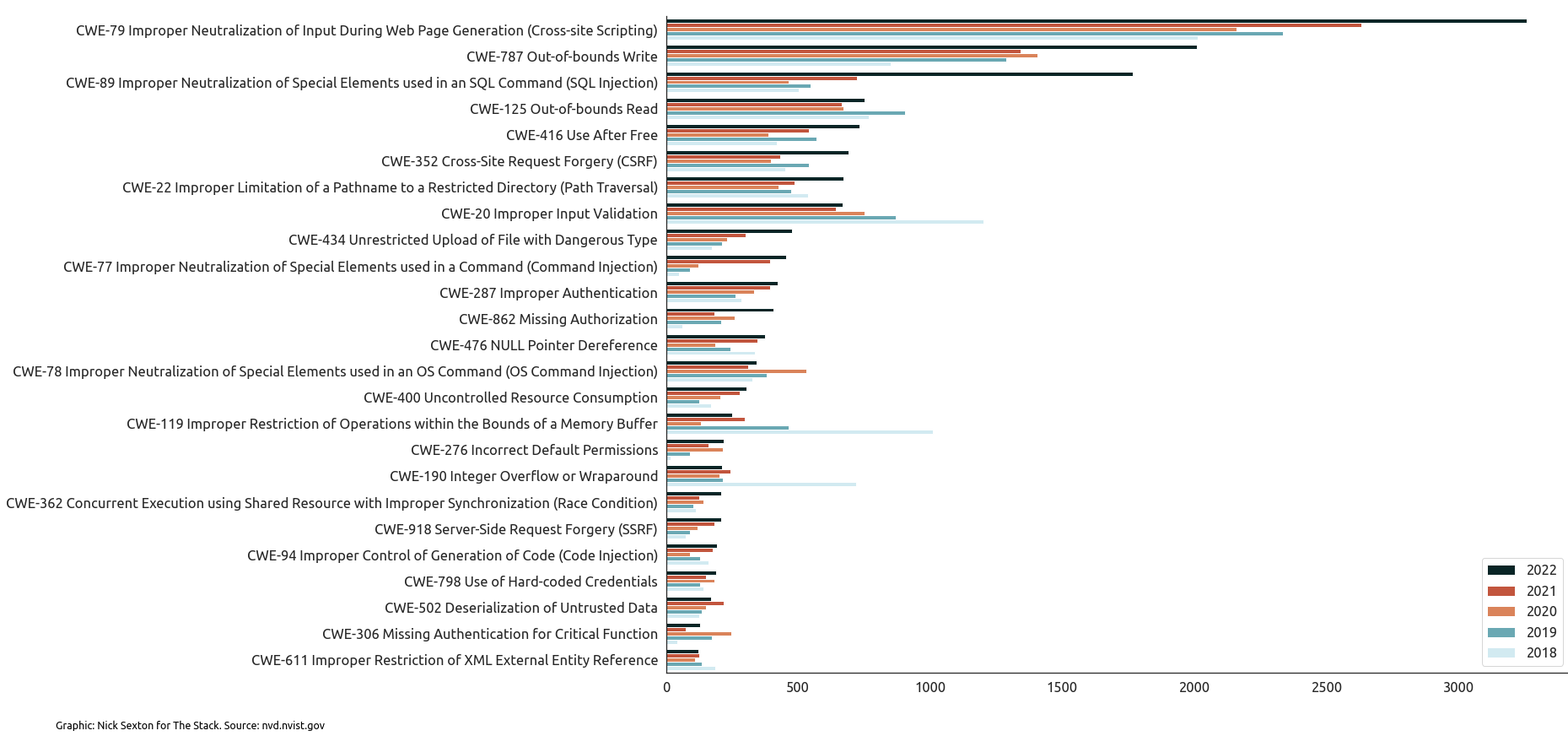
Sweeping supply chain attacks triggered by successful exploitation of file transfer software from Accelion in 2021 also stemmed from a SQL injection vulnerability which some critics might argue effective fuzzing should have identified. The MOVEit Transfer vulnerability has worrying echoes of a pre-auth RCE SQL injection bug in 2021 for the same product.
Progress Software MOVEit Transfer vulnerability
There are some 2,500 instances of MOVEit Transfer exposed to the public internet, Rapid7 said. Attackers with a foothold on corporate environments may also be able to use the MOVEit Transfer vulnerability to access further sensitive files by moving laterally to it.
Progress said in its May 31 advisory that admins should urgently check for the creation of unexpected files in the c:\MOVEit Transfer\wwwroot\ folder on all MOVEit Transfer instances (including back-ups) and unexpected and/or large file downloads and modify firewall rules to deny HTTP and HTTPs traffic to MOVEit Transfer on ports 80 and 443.
| Affected Version | Fixed Version | Documentation |
| MOVEit Transfer 2023.0.0 | MOVEit Transfer 2023.0.1 | MOVEit 2023 Upgrade Documentation |
| MOVEit Transfer 2022.1.x | MOVEit Transfer 2022.1.5 | MOVEit 2022 Upgrade Documentation |
| MOVEit Transfer 2022.0.x | MOVEit Transfer 2022.0.4 | |
| MOVEit Transfer 2021.1.x | MOVEit Transfer 2021.1.4 | MOVEit 2021 Upgrade Documentation |
| MOVEit Transfer 2021.0.x | MOVEit Transfer 2021.0.6 |
The service is the latest in a string of enterprise-scale file transfer services to be hit. Accelion (CVE-2021-27101); Fortra GoAnywhere (CVE-2023-0669); SolarWinds Serv-U (CVE-2021-35211); IBM Aspera Faspex (CVE-2022-47986) have all been successfully attacked in the past 24 months.
