
When you have more than two decades of working as a CISO under your belt, it becomes second nature to listen out for the best advice and lessons learnt amongst your peers. After conferring with security heads from far and wide over the past few months, these were the best pieces of advice given, writes Steve Cottrell, EMEA CTO at Vectra -- who has served as Group CISO at Admiral Group and CSO at Fujitsu, among other roles.
Top lessons for CISO success

Your ISO certificate won’t save you from a breach!
Reaching a certain level of compliance gives a clear sign of progress to the board in a notoriously difficult to measure discipline. But the truth is, you can spend years implementing all 114 of ISO 27001’s controls, and a determined attacker could bypass your defences in a few hours.
Instead, approaches must be THREAT-LED, identifying the organisation’s most valuable assets, who is likely to target it, and prioritising activities to mitigate the identified risks. CISOs should measure security based on their ability to discover if they’ve been breached, using meaningful metrics like mean time to breach when testing security, or the mean time to detect threats. Then, CISOs can work to bring these numbers down to an agreed acceptable level.
In your next board meeting, keep compliance figures as a footnote and focus on the threats your organisations faces and the risks that arise as a result.
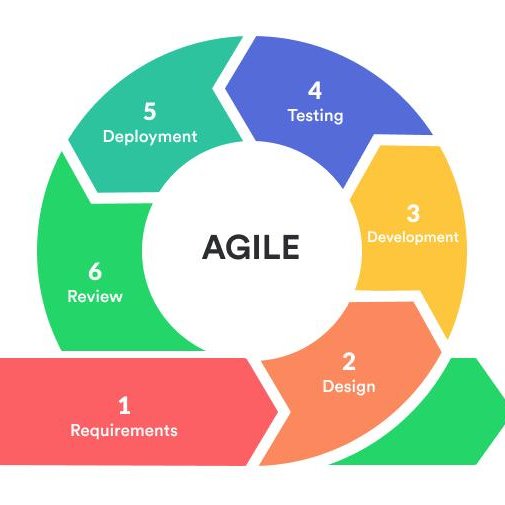
Agile IT isn’t always the answer
In software development, Agile’s “move fast, fail fast” approach can help teams speed time-to-market and remove roadblocks, especially in small organisations and teams. But it doesn’t scale well and won’t always work in all situations for security departments – especially when teams attempt to bypass security and corporate governance to meet their delivery objectives. Care should be taken to choose the best and appropriate delivery mechanism for the task at hand, as it won’t always be Agile.
See also: From C2 to C3 -- Hackers are getting esoteric with exfiltration
Having a very clear governance approach with the appropriate ‘guard rails’, choosing capable tools to help automate security testing , and where possible running regular independent red teams help maximise the chances of success. CISOs need tools that can closely monitor environments, mistakes, and misconfigurations to mitigate risk effectively. The wider business must realise that a product is not complete until all relevant security functional requirements are met, ‘Security’ isn’t simply the approval as one of the final tasks in the sprint. Remember, you can say no if the risks cannot be quantified, or clearly fall outside of the Boards risk appetite!
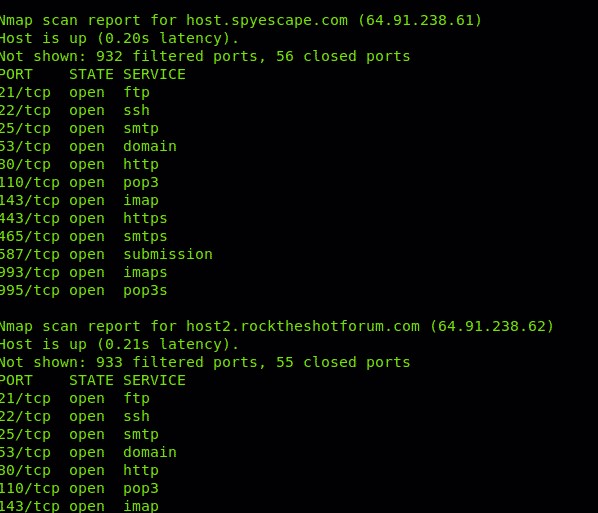
A vulnerability scan simply won’t cut the mustard
Arranging an annual penetration test of point systems is not the same as a comprehensive red teaming exercise. Regardless of maturity, every CISO must be able to offer a clear picture of how their security is really holding up against the latest threat actor tactics, techniques, and procedures.
This means carrying out a threat-led red team exercise, which considers multiple scenarios commonly used by real attackers encompassing people, processes, and technology. Red teaming will offer a considerably better insight into how cybercriminals may attempt to identify and exploit the weakest links in the chain to achieve their objectives (e.g., exfiltration of customer data). It enables the organisation to improve its defences incrementally, by addressing the simplest but most likely route into the organisation from the attacker’s perspective.
With the knowledge gained from a red team exercise, the CISO can prioritise improvement programs to act effectively against real-life risks, spotting left-field gaps that would otherwise be missed in a standard pen-test.

A focus on technical skills alone is holding CISOs back
The CISO position is fledgeling compared to many leadership roles, as such the role has never been clearly defined and every CISO works differently. Most, however, come from a highly technical background, and have been hiring clones of themselves for years. To make the most impact on an organisation, CISOs need to develop soft skills like stakeholder communication and business acumen. If not, they’ll be stuck in the SOC and kept out of the boardroom for another two decades.
Global CISOs, White House, agree 10-point OSS security plan
As each role varies, CISOs should consider this when applying for roles or agreeing the job specification too, making sure they can positively impact their organisation before joining. This means ensuring the role oversees technical tasks but doesn’t necessarily have to execute them, understanding how important security is in the overall business strategy, assessing the maturity of the security programme, and ensuring you have purchasing control. Without purchasing control, it will be difficult to swap old tools for solutions that help drive automation and reduce manual effort.

CISOs must be bold enough to chuck away their old security playbook
Attackers are becoming more organised – constantly tweaking threat vectors, studying widely-used security playbooks, or testing their attacks against outdated security tools. Despite this, 90% of CISOs today still play it safe, clinging to their old playbooks, and relying on legacy technologies like IDPS (Intrusion, Detection and Prevention Systems).
The old ways aren’t working, so CISOs must be brave, throwing their playbook aside and stripping out dead weight. This means taking a threat-led approach, replacing legacy tools with solutions that fit better with data-centric security models to give you better value for money overall. For example, a static signature-based system that throws up thousands of contextless alerts can be replaced with a solutions using behavioural centric approaches underpinned by AI and Machine Learning to spot the riskiest behaviours and flag them up to teams.
CISOs and their teams need to offer service with a smile
As security professionals, we aren’t known for our levity in the office. True, we’re often fire-fighting serious incidents with potentially profound consequences for the organisation, and our career prospects. But our relationships with others are usually characterised by policing and enforcement rather than engagement and support. This needs to change.
CISOs should be getting their teams to build strong relationships, grasp the engineering processes well enough to offer the right tools to the right people at the right time. In fact, they’ll become more like internal salespeople or security evangelists than auditors, getting everyone to buy into security and become more receptive to training and necessary security controls.

Small victories, huge impact
In today’s threat landscape – where cloud and remote work are complicating the IT landscape, and cybercriminals are growing more targeted in their approaches – security leaders are facing more hurdles than ever.
But one thing stays the same. To thrive, CISOs must understand where their key challenges lie, and how to overcome them.