A newly and anonymously disclosed VMware vulnerability in the virtualisation firm’s logging utility lets a remote and unauthenticated attacker execute remote code as a root user (pre-auth RCE) the company warns.
The VMware vulnerability, allocated CVE-2023-20864, impacts VMware Aria Operations for Logs, previously known as vRealize Operations. It has a CVSS score of a critical 9.8. Mercifully it only affects one version, 8.10.2.
It is the second time in 2013 that the software has been exposed to a pre-auth RCE vulnerability, with security researchers at Horizon3.ai in January of this year publishing a vRealize Log Insight exploit POC that chained three vulnerabilities to remotely achieve root on the platform even in default settings.
VMware Aria Operations for Logs bug: Who's exposed?
Other versions of VMware Aria Operations for Logs are also impacted by CVE-2023-20865 but with a lower CVSSv3 score of 7.2. VMware described the vulnerability on April 20, as a deserialisation bug.
Standard disclaimers about not exposing management interfaces to the public internet apply...
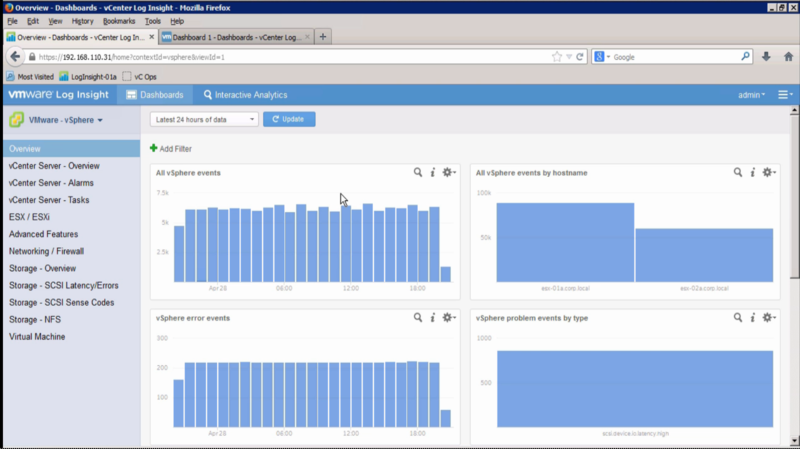
VMware describes Aria Operations for Logs as providing “machine learning-based intelligent grouping and high performance search enables faster troubleshooting across physical, virtual, and cloud environments.”
The utility, available on-premises or as SaaS “can analyze terabytes of logs, discover structure in unstructured data, and deliver enterprise-wide visibility using a modern web interface” it says.
CVE-2023-20864 is the most critical of a series of vulnerabilities in the platform that VMware has urged customers to address swiftly. The US’s CISA also noted that “a cyber threat actor could exploit these vulnerabilities to take control of an affected system. CISA encourages users and administrators to review VMware Security Advisory VMSA-2023-0007 and apply the necessary updates" it added in an advisory late last week.
