
Scans suggest that there are still over 20,000 end-of-life and insecure Microsoft Exchange mail servers sitting exposed to the public internet.
That’s despite vulnerabilities in Microsoft Exchange having been among the Top 10 most widely exploited security vulnerabilities in 2022.
Attacks on the popular on-premises mail and calendering service escalated in 2022 after the prior year’s exposure of a trio of critical vulnerabilities that were so widely exploited, multiple cybercrime groups were spotted contesting access to exposed Microsoft Exchange servers.
(For example CVE-2021-34473, CVE-2021-31207, CVE-2021-34523 or “ProxyShell” in Microsoft Client Access Service (CAS), which usually runs on port 443 in Microsoft IIS, Microsoft’s web server, and which is typically exposed to let users access email via mobile devices and web browsers.)
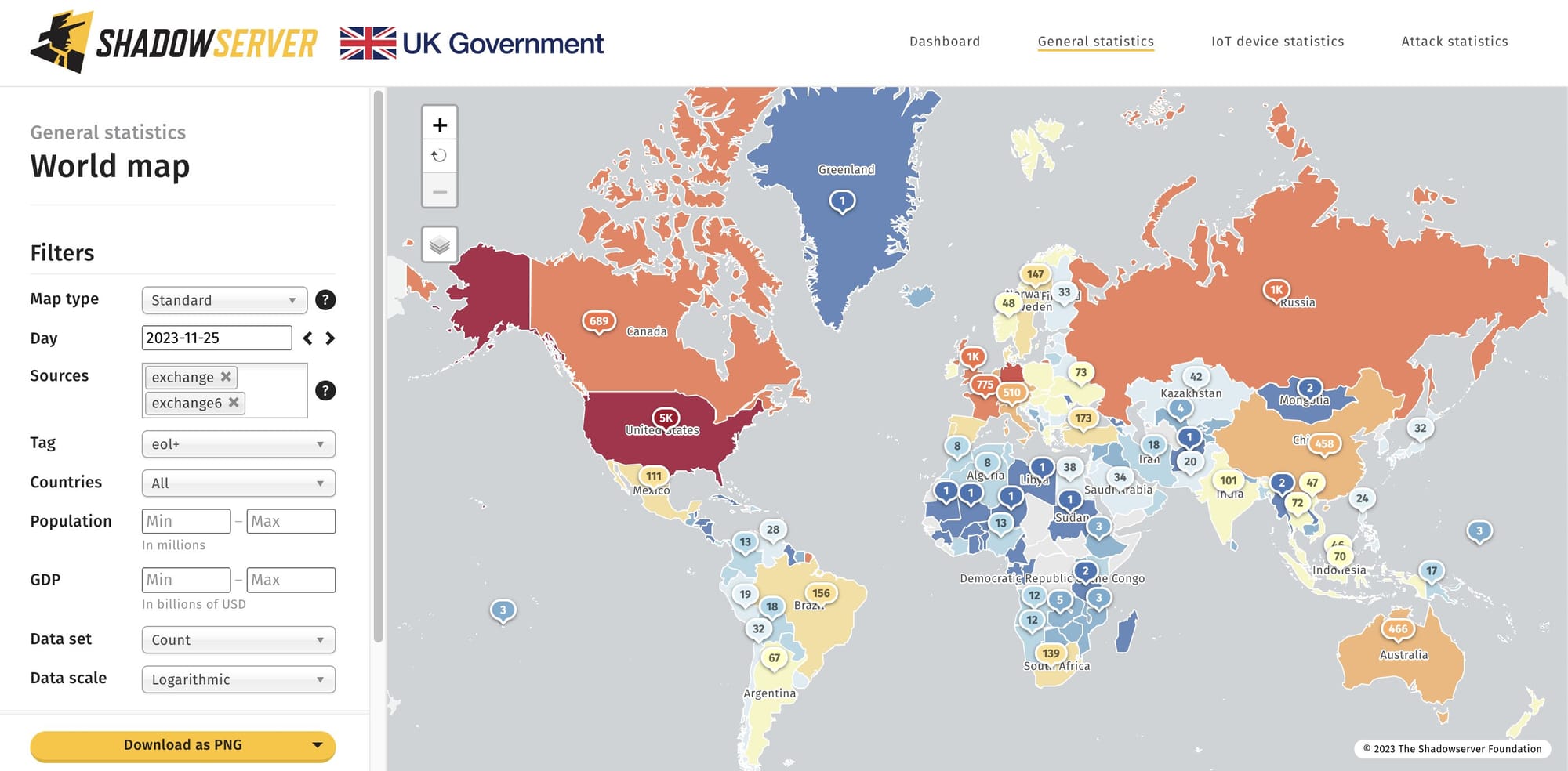
Scans by Shadowserver, an organisation which provides internet security reporting, found 1,094 unique IPs for EOL Microsoft Exchange servers in the UK, 4,742 in the US, and 2,631 in Germany, among other hotspots. Some may, of course, be honeypots; it is unlikely that all are.
Attacks in 2022, noted Microsoft, were so rife that threat groups were observed cleaning up .aspx and .bat files to remove other attackers, and even rebuilding the WMI database by deleting .mof files and restarting the service, as well as using malwareless persistence mechanisms like enabling RDP, installing Shadow IT tools, and adding new local administrator accounts, in a bid to evade incident response efforts that might focus exclusively on web shells, AV scans, and patching.
Those running Exchange Server still should note that as recently as December 2022 CrowdStrike recently discovered a new exploit method (called OWASSRF) consisting of CVE-2022-41080 and CVE-2022-41082 to achieve remote code execution (RCE) through Outlook Web Access.
The new exploit method bypasses URL rewrite mitigations for the Autodiscover endpoint provided by Microsoft in response to ProxyNotShell. The discovery was part of recent CrowdStrike Services investigations into several Play ransomware intrusions where the common entry vector was confirmed to be Microsoft Exchange. Details are here.
Last month (October 2023) meanwhile The Exchange Team asked admins to deploy a "better" patch for a critical Microsoft Exchange Server vulnerability, CVE-2023-21709 and patched during August 2023 Patch Tuesday, that lets unauthenticated attackers escalate privileges in low-complexity attacks that don't require user interaction.
A Q&A on that fix is available here.
Yet another serious Exchange Server vulnerability, CVE-2023-36745 was patched in September. Attackers must be authenticated with LAN-access and have credentials for a valid Exchange user, but with a POC published and at least 23,000 instances exposed as of end-October, it is likely to be added (should it be needed) to the armoury of bugs in the product available for attackers to exploit.
