
Her Majesty’s Government (HMG) appears to be toying with the idea of privatising a significant chunk of the country’s communications interception and data mining apparatus via a landmark £70 million contract.
The Home Office this week said it was exploring “market capability and appetite” to deliver a host of requirements around “sustained access to communications data” for law enforcement and intelligence services stakeholders, as it mulls its future “delivery model assessment” for the sensitive services.
(A delivery model assessment helps officials determine whether to “make or buy” services.)*
The project is being led by the government unit responsible for working with telcos on bulk data retention. (The little-known National Communications Data Service, or NCDS, recently moved its own database and applications to AWS and is currently working on provisioning a "central filtering and results platform" for national internet connection records in the same AWS environment for simple multi-agency access.)**
Communications data intercept proposals led by little-known "NCDS"

This week’s “public information notice” from the Home Office suggests plans to further farm out NCDS and its sister organisation the Data Communications Capability Unit (DCCU) workloads to the private sector.
The two Home Office-overseen organisations are part of a four-member*** entity called the “CDLI Service Partnership” that provides access to Communications Data (CD) Targeted Intercept (TI) and Targeted Equipment Interference (TEI) services to law enforcement and intelligence services under the Investigatory Powers Act 2016.
A market engagement exercise by the Home Office, published May 23, suggests HMG is looking for private sector support not just for a few discretely carved out functions, but management and advisory, architecture, strategic engagement, “succession planning for our people”, user design and a host of other services.
Subject to successful market engagement it expects to "contract with one or more providers to deliver the NCDS, DCCU, and wider CDLI Partnership’s future service needs in relation to Digital, Data and Technology."
Whilst the Home Office no doubt already contracts with numerous software and other service providers as part of its communications data interception and retention requirements, the notice seems to suggest an appetite for significantly wider outsourcing of its needs to a Systems Integrator-type private sector partner.
Big Tech's innovations make it tough for Big Spook...
The move comes as law enforcement and intelligence community challenges continue to mount in the face of a rapidly evolving communications landscape, characterised by shifting telco delivery models shaped by Network Functions Virtualisation; a move away from legacy fixed public switched telephone networks (PSTN); the emergence of smaller telcos; a proliferation of end-to-end-encrypted (E2EE) communications tools; the emergence of technologies like DNS-over-HTTPS (DoH) and more, all amid what the Annual Report of the Investigatory Powers Commissioner recently described as pressure on the law enforcement and intelligence communities to "introduce innovative systems and technologies in response to evolving threats".
A private sector engagement day takes place June 27. The Home Office intends to include "the wider Communications Data and Lawful Intercept (CDLI) Partnership requirements in scope for the future”.
Sustained access to... Whoa, wait, what?
In 2013, Edward Snowden revealed that GCHQ was intercepting people’s private communications at scale. The Investigatory Powers Act 2016 belatedly codified this and set legal guardrails for this activity.
("The analysis of communications data obtained in bulk is a primary means by which the intelligence services are able to discover and assess threats to the United Kingdom. This can only be achieved effectively through the aggregation of data from a wide range of sources acquired and retained under multiple bulk warrants" as the Home Office's 2018 "Bulk Acquisition of Communications Data Code of Practice" puts it, tidily.)
The UK's bulk intercept regime has since come in for numerous legal challenges. In May 2021, the European Court of Human Rights unanimously found that the programme violated of Articles 8 and 10 of the European Convention, which respectively aim to protect the right to private and family life, and freedom of expression.
(The Home Office responded at the time: “The UK has one of the most robust and transparent oversight regimes for the protection of personal data and privacy anywhere in the world. This unprecedented transparency sets a new international benchmark for how the law can protect both privacy and security whilst continuing to respond dynamically to an evolving threat picture. The 2016 Investigatory Powers Act has already replaced large parts of the 2000 Regulation of Investigatory Powers Act (RIPA) that was the subject of this challenge.")
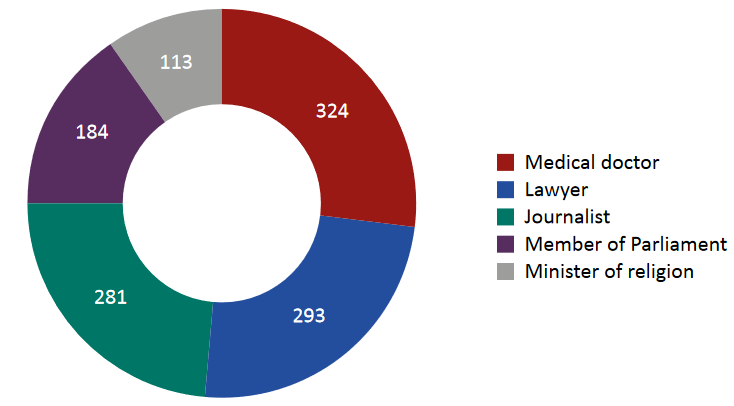
The latest Annual Report of the Investigatory Powers Commissioner, who oversees agency compliance with relevant legislation, revealed in January 2022 that in 2020 communications data was successfully sought for Members of Parliament 184 times, journalists 281 times, and lawyers 293 times. The report notes that "17 authorisations were obtained to confirm or identify a journalist’s source, none of which were urgent. One application was refused by a JC [Judicial Commissioner]."****
To those concerned about the cybersecurity risks posed by what amounts to a backdoor into telcos, the same report noted that "GCHQ has a [legal duty]... to have regard to the public interest in the integrity of telecommunications systems. We tested GCHQ’s compliance with this duty by reference to a specific operational example. Overall, we were satisfied that GCHQ has a robust set of measures in place to ensure any risks to the integrity of telecommunications systems are minimised as far as possible."
"Succession planning..."? How about some sprightly JCs?
The reference in this week's Home Office notice to "succession planning for our people" comes amid as senior national security officials continue to quietly exit the community stage left, whether through burnout, retirement or the calling of more money and lower stress in a less heavily circumscribed world. (As with every other public sector job, salaries are insignificant compared to what they can earn in the private sector. A recent advert for a "Joint Head" of the same NCDS leading this market engagement exercise revealed a salary cap of £85,000.)
Succession planning around data intercepts became an unlikely hot issue around the outbreak of Covid meanwhile. The "Judicial Commissioners" (JCs) who function as a "double lock" and approve warrants for data access often need to travel to secure locations to consider applications. (We dread to think how frustrating this must be for agencies wanting to move fast.) Every single one of the JCs, bar one, was over 70-years-old however.
> Follow The Stack on LinkedIn <
As the Investigatory Powers Commissioner's Office noted earlier this year: "This... senior demographic presented IPCO with a unique business continuity challenge. The Government’s guidance at the time stated the advice on social distancing would be “particularly important” for those over the age of 70 who were classified as 'clinically vulnerable' due to the greater risk of death or serious illness from contracting the virus. It was uncertain whether this advice would change and further restrict the movements of the over 70s or how long the pandemic might persist. A decision was taken that the powers in the Coronavirus Act to appoint temporary JCs should be exercised on the basis that the JCs should not be placed at risk by, among other things, having to travel (often great distances) to attend the office to consider applications in a secure environment" that report revealed.
Strong views on the modernisation/privatisation of intelligence-related capabilities or how the Home Office is handling them? Get in touch by email (alt. Protonmail) or Signal.
Footnotes.
* Or, of course, some complex hybrid of the two...
** The unit is currently seeking a handful of contractors to help with this. It is looking for, quote, a “Product Manager, Scrum Master, Lead Developer, Developer x 2, Dev Ops x 2, Security Architect”. (We hope that this security architect is a bloody good one.) Skills sought include Python, Elastic-Logtash-Kibana, Apache Airflow, and native AWS services like S3, RDS, Lambda, EC2, AWS API Gateway, etc. for those wondering about the stack.
*** We think. The other two being the National Crime Agency's TRACER and GCHQ's 150-strong National Technical Assistance Centre (NTAC), which has also recently advertised for a head of the organisation, on a £83,856 - £92,736 salary.
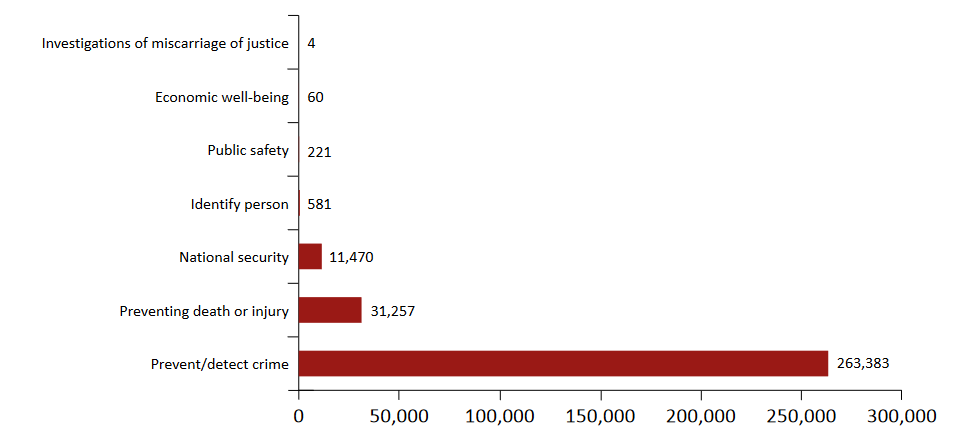
**** Upset by this? Many will be. Strident views here exist on this both sides of the fence, with civil liberties groups regularly decrying what they see as an egregious overreach by opaque agencies that threatens democratic freedoms, and intelligence community staff no-doubt sometimes feeling they are inordinately held back from rapid decision making by policy maker scrutiny, litigation risk, aging technology and even more geriatric legal guardians. Per the table above left. the vast majority of requests for communications data are for criminal rather than natsetc reasons.
