Positive Technologies, a Russian security firm that regularly discloses critical software vulnerabilities to major western companies like VMware, is among the companies and individuals to have been hit with sanctions by the Biden administration this week -- leaving it conceivable that accepting responsible disclosure of the bugs and liaising with the company to receive proof-of-concept exploits could be in breach of the sanctions.
The US Treasury this week described the company as one that "supports Russian Government clients, including the FSB", adding that "Positive Technologies provides computer network security solutions to Russian businesses, foreign governments, and international companies and hosts large-scale conventions that are used as recruiting events for the FSB and GRU." (Respectively, Russian civilian and military intelligence agencies).
The Treasury sanctions "generally prohibit all transactions by U.S. persons ... that involve any property or interests in property of designated or otherwise blocked persons. The prohibitions include the making of any contribution or provision of funds, goods, or services by, to, or for the benefit of any blocked person or the receipt of any contribution or provision of funds, goods, or services from any such person."
The Stack has asked the Treasury, but could not immediately confirm/disconfirm that receiving a bug disclosure would be considered receipt of a service. We'll update when we get an answer.
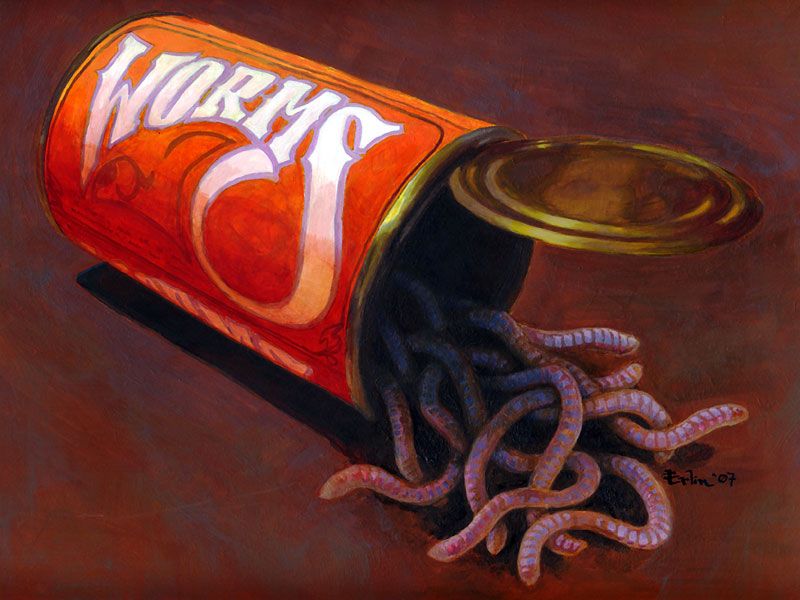
The move has raised some deeper troubling questions.
Positive Technologies claims more than 2,000 customers in 30 countries, including BT, ING, Societe Generale and Samsung. The company said Friday it denies the "groundless accusations", adding that "our researchers detect hundreds of zero-day vulnerabilities per year in IT systems of various classes and types. All of the vulnerabilities found, without exception, are provided to the software manufacturers as part of the responsible disclosure policy and are not made public until the necessary updates are released. Each such research is highly evaluated by the system manufacturers and is used to increase information security of their final product."
(The company has reported a trio of critical vulnerabilities in VMware software this April alone -- including most recently a critical bug, CVE-2021-21982, in the company's endpoint protection platform.)
Troublingly, given the US's allegations, Positive Technologies has long enjoyed security partnerships with companies like IBM and Microsoft, the latter which had it listed until this week as a partner of its "Microsoft Active Protections Program" (MAPP) -- a programme that gives customers advance access to vulnerability information to ensure faster patches for their clients. As Microsoft notes of MAPP, "this includes the steps used to reproduce the vulnerability as well as the steps used to detect the issue. Periodically, Microsoft might also provide proof-of-concept or repro tools to further illuminate the issue and help with additional protection enhancement, as long as this information enables software security providers to provide timely and enhanced protections..."
Critics say if these were passed on to US adversaries like Russian intelligence, they could have been reverse engineered and abused before most companies patched. Ben Hawkes, a technical lead at Google's Project Zero was among those raising concerns, alleging on Twitter that "MAPP has consistently been leaking to attackers since inception." (Despite geopolitical tensions with China being at a sustained pitch, the country considered a "strategic adversary", and China's National Security Law explicitly coopting the private sector into espionage efforts, Microsoft continues to include numerous Chinese companies in MAPP.)
Hawkes suggests Microsoft move trusted partners "to the 24 hour notice tier, and provide guidance to everyone else after the patch is released." Microsoft has yet to comment on the debate.
Positive Technologies, meanwhile, says "geopolitics should not be a barrier to the technological development of society and we will continue to... protect and ensure cybersecurity around the world [and]... work under normal conditions, in full compliance with all of our obligations to our customers, partners, and employees." It's just that some of these, of course, may well be Russian intelligence.
Among those weighing more broadly into the sanctions move was the co-founder of US cybersecurity firm CrowdStrike.
Pointing to the views of Deputy National Security Advisor Jonathan Finer, who as argued that "no single action that we will take or could take in and of itself could directly alter Russia’s malign behavior", CrowdStrike's Dmitri Alperovitch asked "What are we hoping to accomplish with the #Russia action today? Apparently it’s not a change of their behavior... I am not at all opposed hitting back at Russia. They certainly deserve it. But the action, in my view, should have been targeted at very specific behavior we find most egregious (ex use of chem weapons) with a built-in off-ramp that if we observe change, the sanctions will drop."
Strong views on this? Get in touch, we'd love to hear them.
