
The Open Source Security Foundation (OpenSSF) has inducted 13 new members, including CapitalOne and Akamai, as a senior Linux Foundation director warned industry that secure development practices remained a chimera, saying “we're not teaching our developers anything [about security]... we have an endemic problem."
CapitalOne joins OpenSSF as a premier member, while Akamai, Indeed, ZTE, Kasten by Veeam, She Bash, Socket Security, Scantist, Sysdig and Timesys joined as general members. Eclipse Foundation, Purdue University and Todo joined the foundation as associate members, OpenSSF confirmed this week.
Founded in 2020, and supported with funding from the Linux Foundation, OpenSSF brings together organisations including Google, Microsoft, IBM, NCC, OWASP Foundation, JPMorgan Chase in an attempt to tackle pervasive security issues across the software supply chain amid a growing industry bid to "shift left". OpenSSF replaced previous initiatives such as the Core Infrastructure Initiative and the Open Source Security Coalition.
David A. Wheeler, director of open source supply chain security at the Linux Foundation, told The Stack the new members would bring vital expertise and resources to OpenSSF: “Each of these organisations is depending on it and putting a little bit of time and effort, membership funding, bringing some of their own people, their own experts to the table. It means that with a little bit of that, when you pull it together, we can do a whole lot.”
‘We're not teaching our developers anything’
He said improving education and best-practice across the software industry was vital: “How did we get to this place where so much software, both open source and closed, has so many vulnerabilities?
"And this is not an open source unique problem, this is a software problem. And the short answer is, we're not teaching our developers anything, and so we're getting better software than we deserve..."
“The good news is that open source is reviewable. That's awesome, it's a really big advantage.
See: Global CISOs, White House, agree 10-point open source security plan
"The challenge is, a lot of those reviewers don't know how to develop secure software, either. It's the weakness in any peer review process – you're assuming the reviewers have knowledge of what to do. And we have an endemic problem of not enough people knowing how to develop secure software,” Wheeler added.
He said the Linux Foundation faces the same hiring challenges as the rest of the industry: “You'll be shocked to know that in the computer security arena, it's really, really, really hard to hire all the expertise.
“But one of the ways, frankly, to try to get all those different people with that expertise is basically by getting together the organisations that already employ them. Step two, they've got different reach in different organisations, can give their perspectives and also can help us identify where the challenge is.”
Members such as CapitalOne, in highly regulated industries, bring a vital perspective on secure development and supply chain security according to Wheeler. And he also noted the importance of the funding new members bring to OpenSSF, enabling it to expand its operations.
“Every time we enrol members, we have more money to focus to spend to actually address the problem. We can take funding for many, many folks, fix a particular issue – and now it's fixed for everyone. And we can do this over and over, we're going to get very good at this thing.”
The libNebraska problem
According to estimates from 2020 and 2022 studies by Synopsis, somewhere between 70-90% of any software stack is open-source software – and much of this is used without being interrogated or investigated by developers, according to Wheeler. But as the Log4Shell incident showed, flaws in under-appreciated open-source projects can have devastating effects.
“When you are a customer, what you see is, here's a product that solves a problem. When you are the developer, you see what's called your immediate dependencies, or your direct dependencies. Oftentimes, it's possible to list what's called your indirect dependencies. But in many, many cases, they're mostly invisible,” said Wheeler.
“Yes. If you watch carefully, you can see debug information that will tell you, yes, I'm downloading these 3000 other things right now. But it's not at all unusual today. For example, if you start a web front end application using something like React, I think it's something like 700 direct and indirect dependencies for an empty React project.”
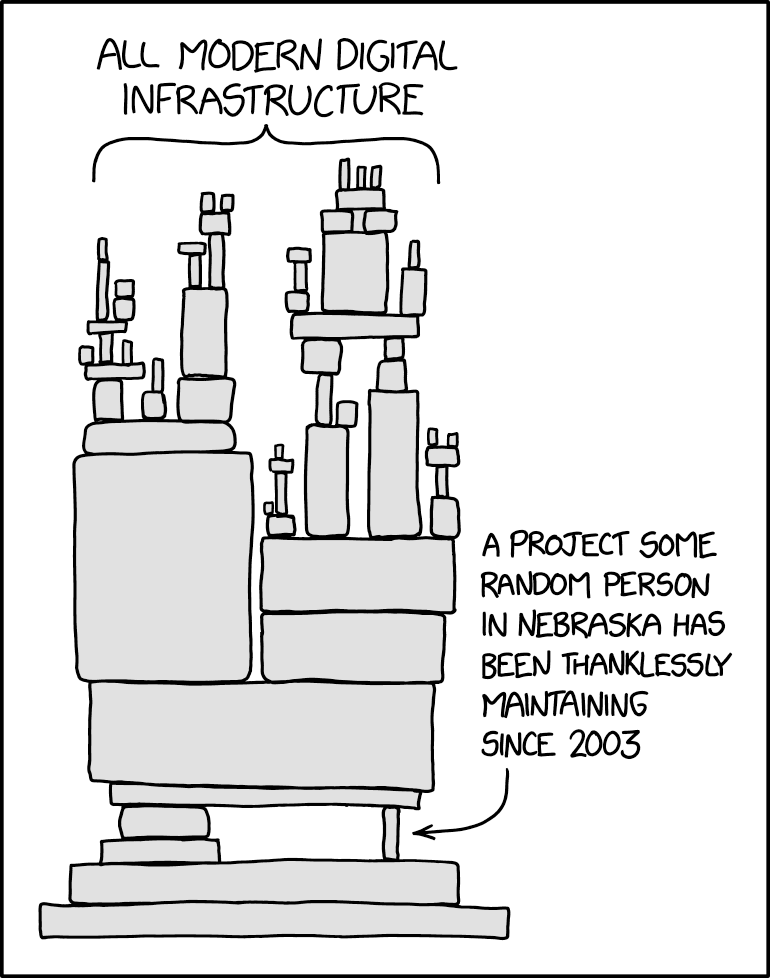
The problem is neatly illustrated by an xkcd comic from August 2020, which according to Wheeler has become famous in the open-source world: “In the technical community, this is often called the libNebraska problem.”
He noted the strip exaggerates for comic effect: “But it is a real thing, there is real truth in that cartoon – if you look down the stack, not everything is equally able to sustain the load that it's being asked to take. I think it's important to understand how things look from a developer or a customer organisation. The fundamental problem is they don't see those layers. And so it's very easy for the libNebraskas not to get noticed now.”
The 10-point Open Source and Software Supply Chain Security Mobilisation Plan, announced by OpenSSF, the US government and stakeholders across the industry in May 2022, is intended to help tackle this problem, among many others.
One of its 10 streams is to develop a risk-assessment dashboard for 10,000 open-source components – another is development of a team to help maintainers of the world’s libNebraskas.
See: Global CISOs, White House, agree 10-point open source security plan
Wheeler emphasised the blame for issues with open-source projects – such as the Log4Shell vulnerability – shouldn’t fall on individuals: “I think we do have to be careful that there are humans on all ends of this. They make mistakes. We're probably not going to eliminate all the humans, but what we can do is ask, do they know what they need to know, have they received some training, are they taking proper steps, like using tools to detect common problems?”
He also said the best approach to more secure development will ensure that a rising tide floats all ships: “The libNebraskas are a particular concern – and really, since you don't always know which ones are going to have problems, as much as possible we’re trying to raise the floor for everyone.”