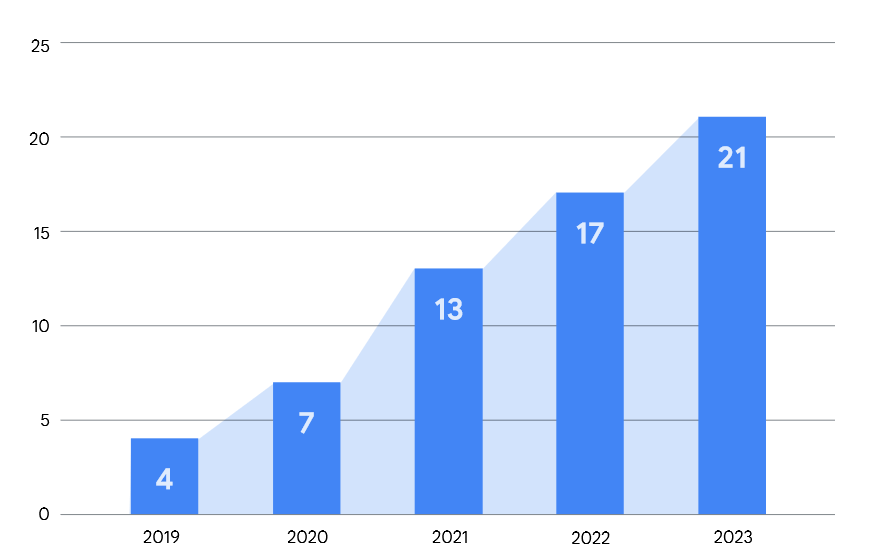
Zero day exploitation by Commercial Spyware Vendors and their clients is rising sharply – accounting for “half of attributed zero-day exploitation by government actors” in 2023, according to a new report by Google; with Chinese APT-backed zero day exploitation dominating over other states.
The joint report by Google’s Threat Analysis Group and Mandiant, explores the abuse of zero days (previously unknown and unpatched software vulnerabilities) and emphasises that the two are seeing an “ increase in enterprise-specific technologies being exploited” in the wild.
Notably, in 2023, there were “no in-the-wild zero-days detected that targeted macOS. While some of the iOS vulnerabilities also affected macOS due to their shared kernels and other components, the discovered exploits were only targeting iPhones,” they said – in a chart flagging a series of iOS exploits believed to have been developed by the US’s NSA.
See also: Kaspersky burns 11,000-line “NSA” exploit: Calls 14-step iPhone attack “definitely the most sophisticated attack chain ever seen”
Critically, attackers are targeting zero days in third-party components and libraries that allow them to then attack multiple products.
TAG and Mandiant highlighted Chrome vulnerability CVE-2023-4863 and Safari vulnerability CVE-2023-41064 as “actually the same bug”, for example; this also affected Android and Firefox.
CVE-2023-5217 was another zero day that affected more than one browser. It stemmed from a bug in libvpx,a VP8/VP9 video codec library.
This vulnerability affected Chrome, Firefox, iOS, and Android, whilst two in-the-wild zero-days (CVE-2023-2136 and CVE-2023- 6345) in Skia, a 2D graphics library used by Chrome, ChromeOS, Android, and Firefox.
The two could attribute the motivation behind 58 of the 97 zero day exploitation incidents they tracked in 2023: 48 exploits suggested espionage actors were at work, 10 “financially motivated” cybercriminals.
See also: Massive “i-Soon” leak reveals Chinese firm's hacking tools, targets, including NATO
With increasingly remote workforces, despite many return-to-office mandates, mobile devices are a critical threat surface – and with over three billion Android devices active in the world, it’s a big target.
TAG and Mandiant noted that the majority of Android zero days that came under attack in 2023 stemmed from GPU driver vulns (last year this included two in Arm’s Mali GPU and three in the Qualcomm Adreno GPU driver), giving attackers “coverage for many different devices from different manufacturers,models, etc. with only two different exploits…”
“In addition to common platforms such as Windows, Android, iOS, Chrome, and Safari, we saw a few other applications targeted with in-the-wild zero-days: WinRAR, Adobe Reader, Microsoft Word, and Microsoft Outlook,” Google and Mandiant said in their report.
