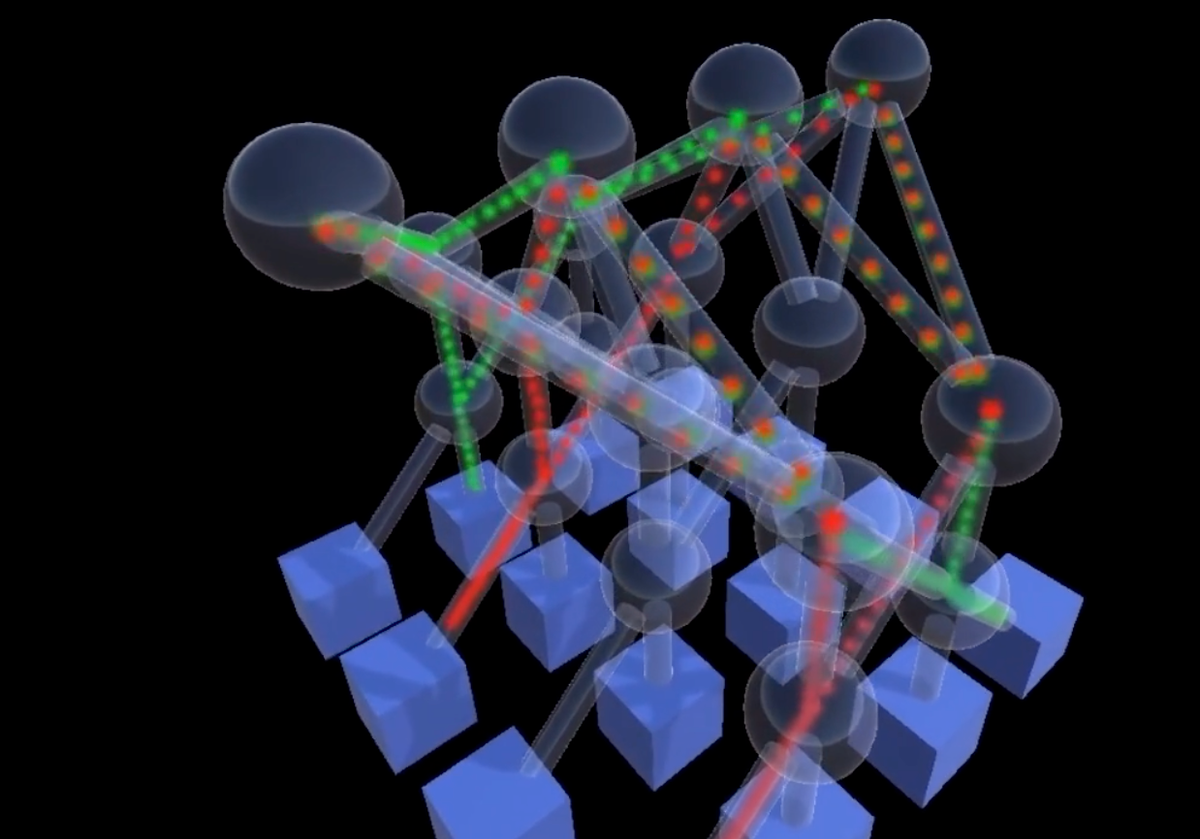
130,000 GPUs connected with just two tiers of switches.
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest
You say "potato", I say sending data across a proprietary global network kept with an intentionally low network utilisation rate is not an act of charity...

Worldpay -- "a dozen payment M&A deals in a trenchcoat" -- will find a new home in the warm embrace of private equity after investment failings.

"... a concept has been developed for a centralised solution that will provide firms with an automated classification answer."

As well as setting up honeypots to identify and target brute force attacks, the NCSC also took down 24,407 web shells in 2022.

If AI creators use a ‘three laws’ approach, building in security by design, following secure AI guidelines and frameworks, AI may live up to some of the hype...

Some data transformation failures are "inherent to what you're trying to do, which is discover insights; knowledge generation is not a deterministic process. But some of that is also because people don't know how to do it..." he tells The Stack.

"This change will multiply the number of certificates organizations need to manage by at least five times..."

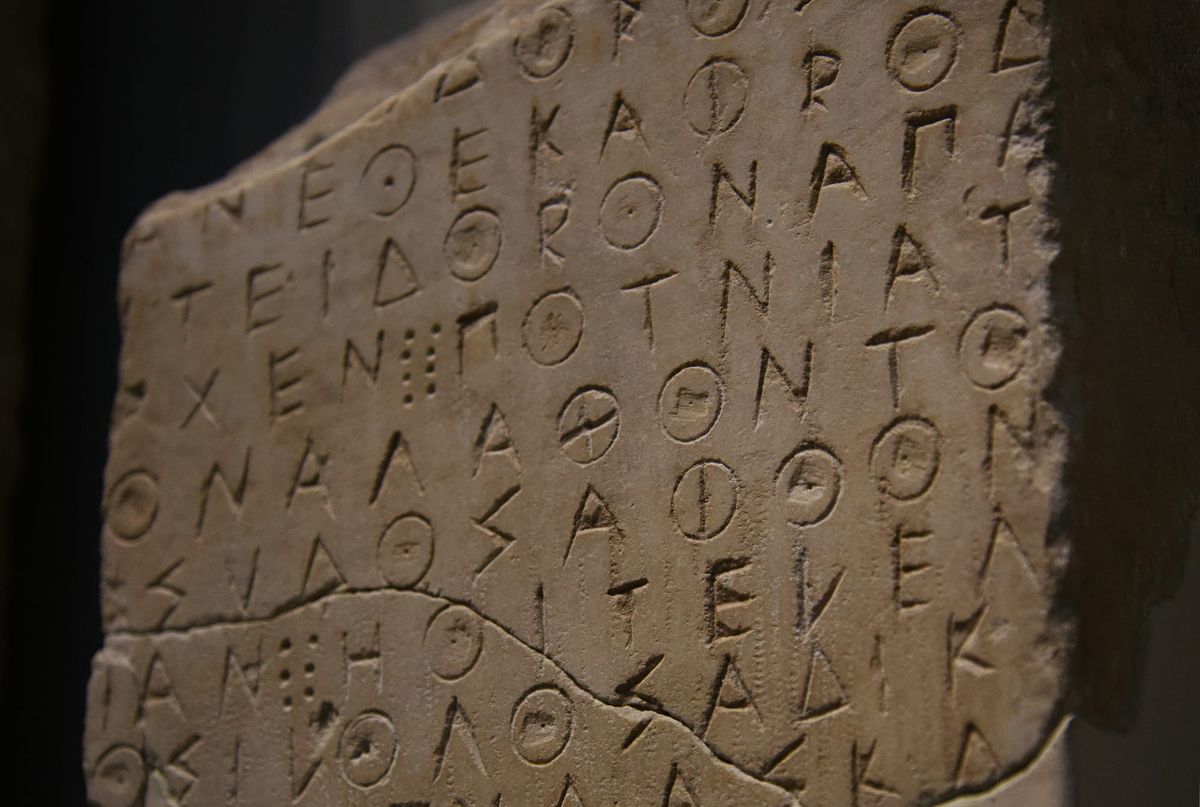
Financial transactions, medical records, and national security secrets. The cornerstones of our digital world are closely safeguarded by intricate cryptographic systems. These systems, which have been the backbone of our digital security for decades, are integrated into every aspect of our lives. However, as we inch towards the era of