A critical vulnerability in F5’s BIG-IP Access Policy Manager (APM) is being exploited in the wild. The bug, allocated CVE-2025-53521, gives a remote attacker unauthenticated remote code execution (pre-auth RCE) powers. IOCs published by F5 today point to sophisticated attacks in which the threat group is disabling the SELinux
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest
Congress was warned that holding back compute will not stop China's accelerating AI and the global adoption of its models.

Nobody else wanted to migrate myriad ageing HP-Unix, IBM AIX, Sun Solaris, VMware ESXi, Windows, MWG-MLOS, and NetApp ONTAP applications off Fujitsu data centres?

Enterprise-targeted surveillance processes "tens of millions" of posts a day, and Gemini is smart enough to avoid false positives, Google swears.

"There is no longer a meaningful boundary between the kinetic and cyber threat surfaces."
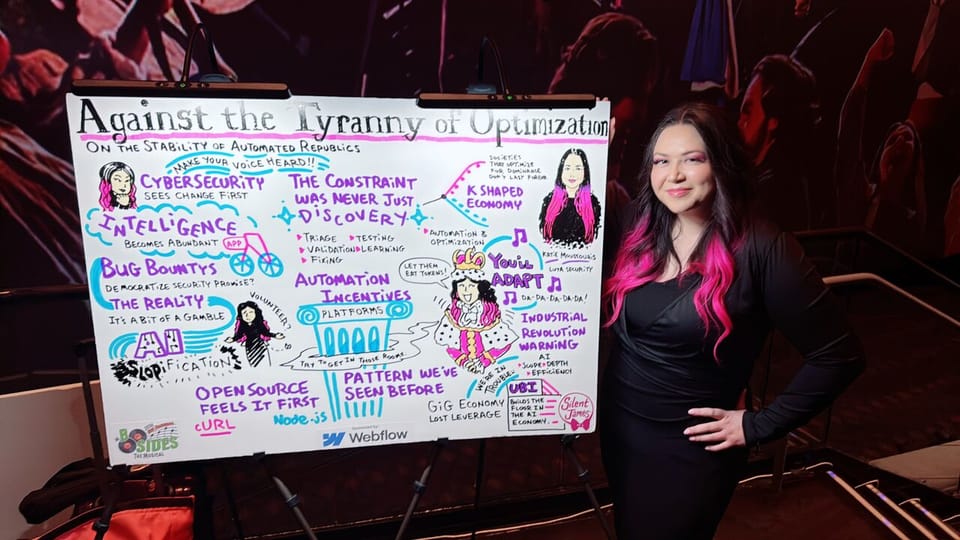
Katie Moussouris calls on security researchers to sandbag human-in-the-loop processes against AI automation.

Hackers continue to have success at hiding malicious processes in VMs – that launch at startup but hide from EDR processes. The behaviour is not new, but deserves renewed attention. Fresh examples of its use as an attacker technique come from Microsoft, which has seen this behaviour during attacks on exposed
























