AI is speed running virtualisation and cloud computing, but how do you isolate for security and still get enough information to make good decisions?
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest
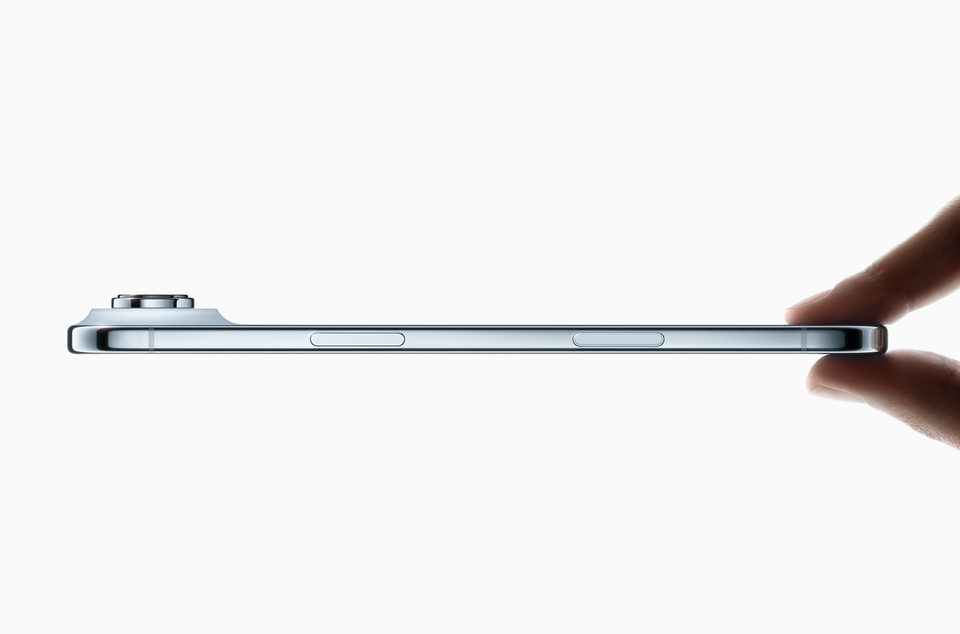
There's no room for SIM cards in the new iPhone – which has wider implications for telecoms

"The explosion of content creation and automation in the enterprise...and LLM advertising are a massive opportunity for Adobe.”

Dassault Systèmes software used by major manufacturers including Boeing supplier.

While Microsoft, already in the system, gets an easier ride on general AI and Israel concerns.

"Utility scale" quantum computing facilities are within reach, says now $7 billion startup.

OpenAI reportedly makes up 95% of the new contracts that gave Oracle an epic value spike.