New hires, especially coders with deep access to vulnerable systems, remain a prime vulnerability. Exploited mostly by North Korea – for now.
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest
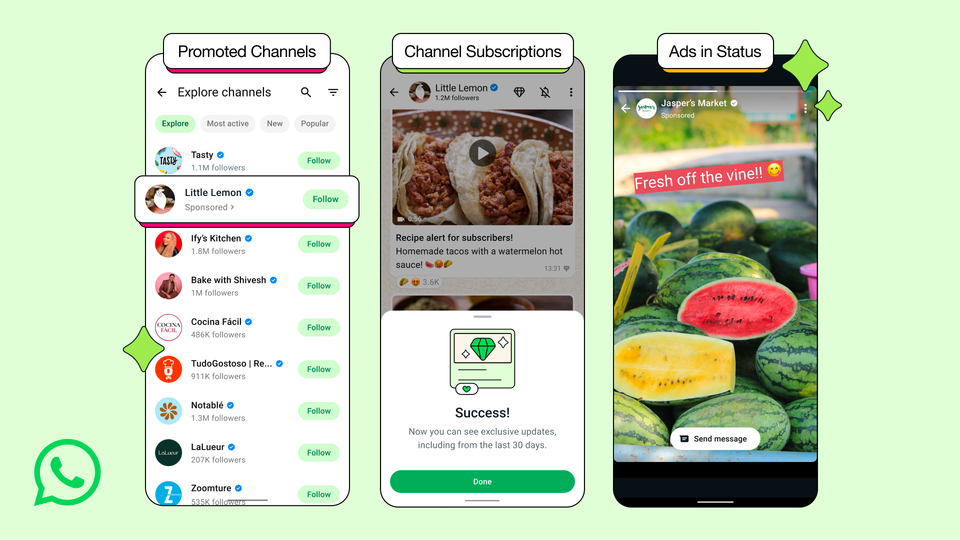
"Our ads will appear in the Updates tab, in Status and Channels, where people are open to discovery"

"Many vendors also have slightly different licensing rules around non-production environments, and SAM tools do not have the capability to detect server environments without manual configuration, or by connecting them to a company's CMDB to gather that data..."

"If this had been flag protected, the issue would have been caught in staging"

Her appointment comes amid deep parliamentary concern that there is “£3 billion of public money being spent for which there is no oversight capability.”

"You read all these scary statistics and it just doesn’t seem to be getting any better."

GCP promises in future to "prevent metadata from propagating globally without appropriate protection, testing and monitoring in place."

"We have to make sure we’re building a team where people are happy to work"























