New hires, especially coders with deep access to vulnerable systems, remain a prime vulnerability. Exploited mostly by North Korea – for now.
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest

Little sh*ts use social engineering techniques to get Salesforce extension "Data Loader" installed then plunder material from targets.

"Anyone can use an ISV to run their business, but that doesn't give them a competitive advantage..."

"There's been a significant trend over the last couple of years back to disaggregated infrastructure..."
"A leader who works relentlessly to understand our customers’ security needs"
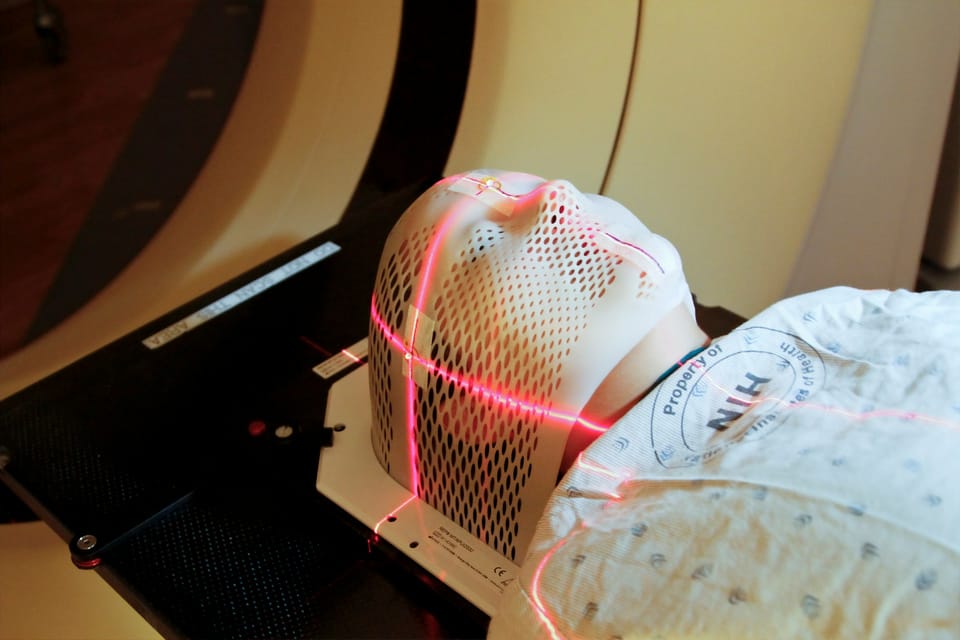
Current algorithms too limited, SaaS too pricy and too hard to validate in a fast-moving AI world says leading radiologist. Royal Marsden is now testing its own...

New parent company, EU staff, technical autonomy all on offer to keep concerns sedate.

Government says it will take a new approach to defence spending in response























