“A very stable and straightforward exploit” across distros, developed after Xint Code pointed an LLM at the Linux kernel for “about an hour”
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest

"At the end of March 2024, there were 116 whole-force skills pinch points assessed as significant or above..."

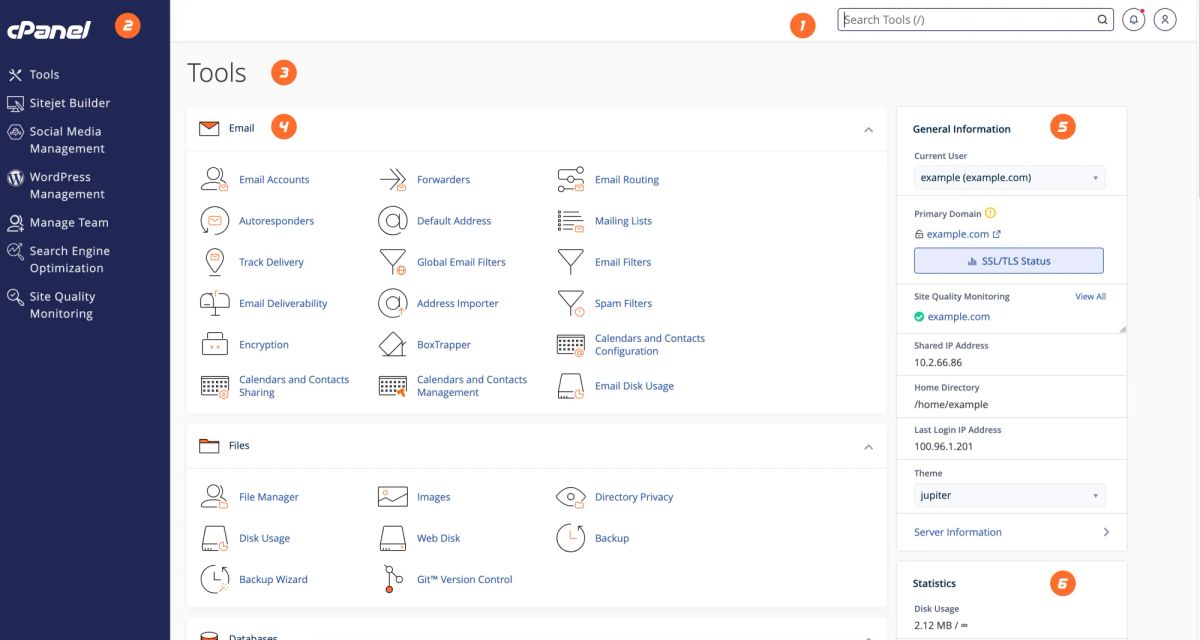
Streamlined authentication, monitoring of LLM use across multiple models? Holy Terminal, Batman, why buy it when build it and open-source it never went out of fashion.

Redmond pushes fixes for 117 vulnerabilities, three rated critical, five as publicly known , and eight marked as “exploitation more likely.” Beyond Microsoft, there are...

No shock and audits says pure play Java specialist, with extended support for Java 6 and 7, and open source roots.

Billions in shared services and ERP harmonisation work out to market across four HMG programmes, with Cognizant, Workday the first big winners.

The National Cybersecurity Centre offer some useful ideas on how to speak in language executives will understand and persuade it to take security seriously.
Attackers called AWS console-only APIs after nabbing key to call Bedrock model, used "common jailbreak techniques to bypass model content filtering" says Permiso