A critical vulnerability in F5’s BIG-IP Access Policy Manager (APM) is being exploited in the wild. The bug, allocated CVE-2025-53521, gives a remote attacker unauthenticated remote code execution (pre-auth RCE) powers. IOCs published by F5 today point to sophisticated attacks in which the threat group is disabling the SELinux
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest

IBM is providing a custom "Asset, Configuration, Patching and Vulnerability” service with a special focus on vulnerability management.

A CVSS 9,8 bug that lets attackers spoof legitimate connectors between Microsoft/Azure services is the pick of the bunch...

Starting when? Starting now. Kiss goodbye to support and subscriptions (SnS) on-premises users, too.

"If spot instances weren’t available, we had no way to tell Cluster Autoscaler to fall back to on-demand Instances, and we ended up stuck in a few loops…" others note.

Hammer down those AWS bills, chisel away at that scheduling latency; pick a carpentry tool, pick your clumsy metaphor...

“I think that willingness to let a third-party run it where they don't necessarily have the direct operational control. It's just a much higher bar…”
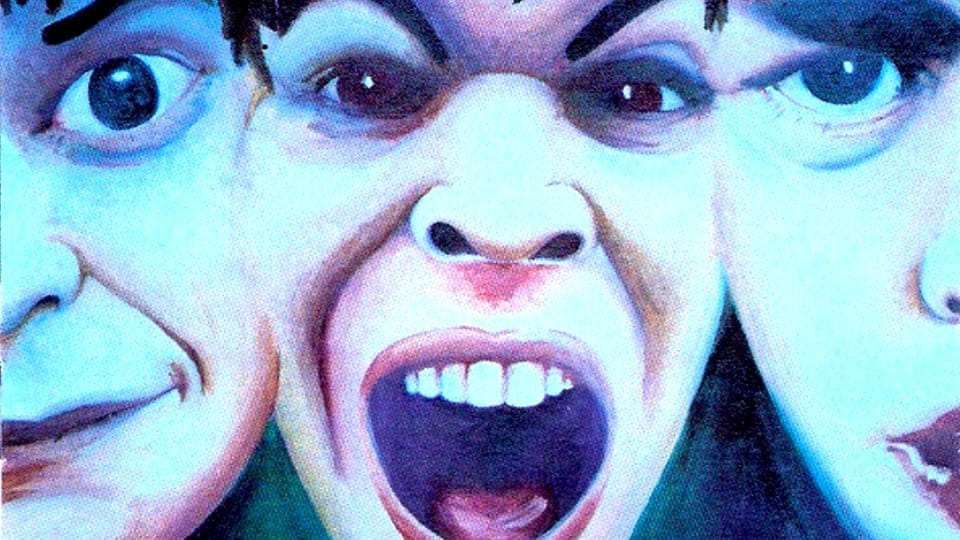
You're probably exposed to rootkit risk, because vendors wanted their logos to show during boot processes -- everything's broken, howl into the abyss, why's this security advisory on a domain like https://9443417.fs1.hubspotusercontent-na1.net anyway?























