A critical vulnerability in F5’s BIG-IP Access Policy Manager (APM) is being exploited in the wild. The bug, allocated CVE-2025-53521, gives a remote attacker unauthenticated remote code execution (pre-auth RCE) powers. IOCs published by F5 today point to sophisticated attacks in which the threat group is disabling the SELinux
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest

Big claims by Satya Nadella, big news for the industry, but no benchmarks or hard specifications yet.

"Loaded by default on just about every version of Windows, so it provides a broad attack surface"

You filthy animals are **** at network architecture, and it may be "necessary to expand threat hunting" says NCSC.

"You have to be intentional about designing for real people who are not security experts."
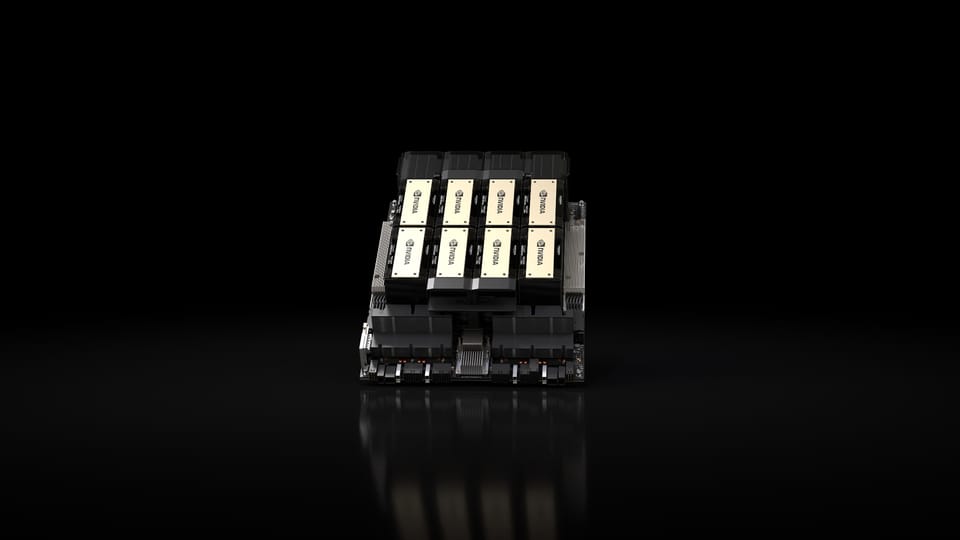
An eight-way HGX H200 provides over 32 petaflops of FP8 deep learning compute and 1.1TB of aggregate high-bandwidth memory

A big ERP overhaul, sustaining app-led revenue growth and a focus on supply chain optimisation are priorities at Nike...
"Once an attacker is past the initial access, the opportunities are ample for lateral movement and privilege escalation within a cluster..."
"We operate with the assumption that a sophisticated nation state threat actor is always active inside the organisation"






















