“A very stable and straightforward exploit” across distros, developed after Xint Code pointed an LLM at the Linux kernel for “about an hour”
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest

"RFPs now look much more thought-out: Cloud security is very much established in most CISOs’ minds as a category.”

Gradio by Hugging Face, Jupyter Server, and Streamlit from Snowflake vulnerable to NTLMv2 hash disclosure of the kind recently exploited by... CISA

"Tiny Time Mixer models are state of the art in terms of performance and can be run on a laptop with an Apple M1 or M2 processor.”

"To attract a competitive outsourced strategic partner… the MPS should position itself as a progressive and reforming organisation"

CEO admits need to be “more proactive about having the security conversation” in wake of customer breaches
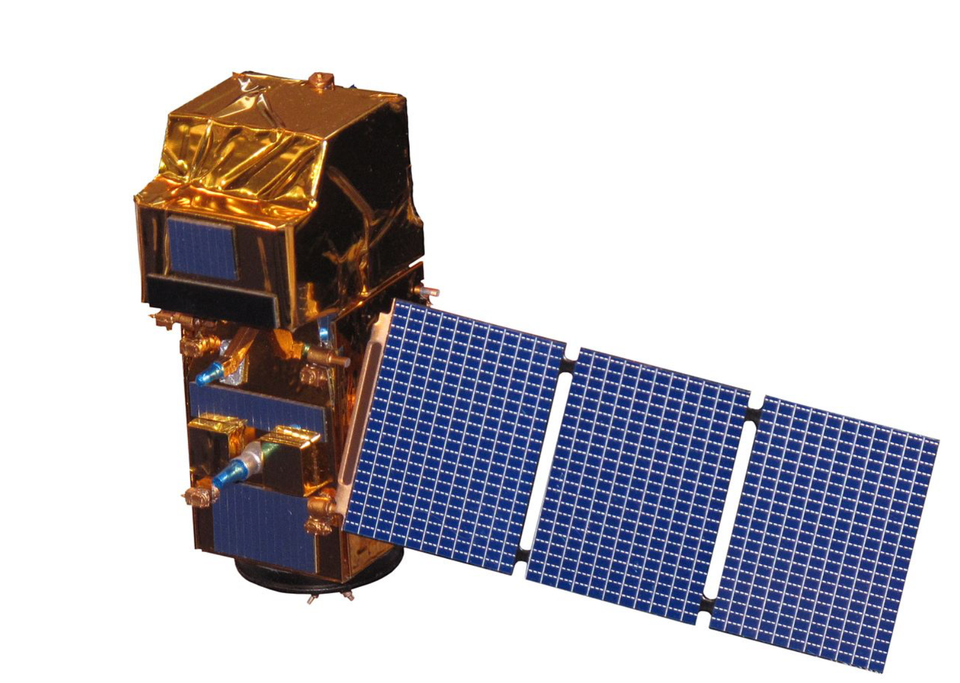
"We have a fast-growing space sector in the UK but for too long we have struggled to tap the huge potential of satellite data to drive positive change in the real world."

"For us, GenAI is an efficiency play. We're moving the needle and helping our lawyers become more effective."